Configuring VPN connections with Linux clients
Enabling GRE Support
If you're trying to connect a VPN client to a Microsoft PPTP connection and you are using a Linux box as a firewall for your broadband connection, you'll have to take an additional step. Allow Generic Route Encapsulation (GRE) protocol to pass through the firewall. If, for example, you are using iptables on your Linux firewall and your VPN server has the IP address 189.44.45.3, you would enter the following:
iptables -I FORWARD -p 47 -d 189.44.45.3 -j ACCEPT
Routing Packets through the Connection
Sometimes you'll find it necessary to explicitly route packets through a specific interface. Many Windows administrators consider this one of the biggest challenges in working with Linux clients.
The need for explicit routing is especially important when your remote network is using public IP addresses. Even though you have a VPN tunnel, your network interface might still try to route packets across the Internet, rather than through the VPN tunnel. Many times when I have helped troubleshoot "failed" VPN connections, all I had to do was simply add a few alternative routes to the default routing table. Sometimes I would do this with the route command (as root). Other times I used the VPN GUI application.
The route command is the standard:
route add -net 13.163.97.23 netmask 255.255.255.255 dev ppp0
Also, you can use the ip command
ip route add 171.87.44.54/24 dev ppp0
or specify the routes with the use of the VPN software GUI interface. In some cases, if you don't add these routes, the packets that you intended to go through the VPN tunnel will be routed through your wireless or Ethernet card instead of your VPN interface.
GUI Options
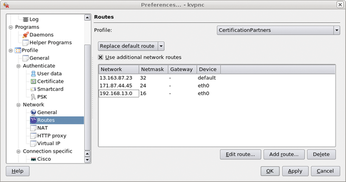
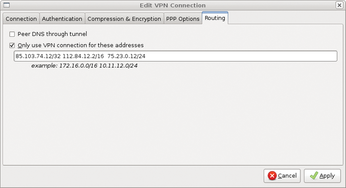
The GUI VPN applications are getting much better at adding routes on their own. Figure 1 shows the settings for KVpnc. Figure 2 provides a similar configuration in NetworkManager.
As these images show, packets that match the IP address and subnet mask will not be sent across a standard network connection; rather, they will be sent through the VPN tunnel.
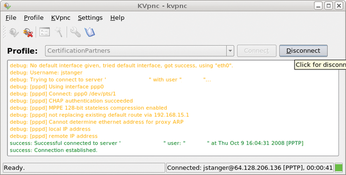
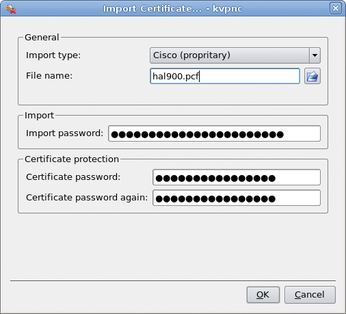
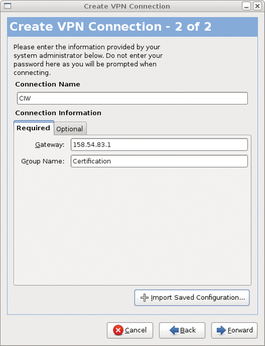
KVpnc (Figure 3), which is supported by many distributions, is perhaps the most versatile client in that it supports L2TP, Cisco free and proprietary VPN protocols, and OpenVPN and Microsoft PPTP. KVpnc also lets you import certificates, as shown in Figure 4.
Even though the user interface programmers can't spell particularly well (notice the word "proprietary" is misspelled in my version of the program; Figure 4), the KVpnc team has created an implementation that works particularly well with Cisco devices.
The venerable pptpconfig tool also is available with many distributions. The key to getting pptpconfig to work properly is to make sure the encryption settings are configured exactly as your network administrator has them set.
I've often found that requiring MPPE encryption and enabling stateful MPPE encryption are important. In the case of pptpconfig, you would select "Require Microsoft Point-to-Point Encryption (MPPE)" and "Refuse Stateless Encryption" to accomplish this.
Pptpconfig also has the ability to add routes automatically. Simply click the Routing tab, then select the Client to LAN radio button and enter the routes of the systems you want to connect with through your VPN tunnel.
Many Linux users prefer the NetworkManager client for one simple reason: It tends to work. Plugins are available for NetworkManager that support various protocols, including OpenVPN, Microsoft PPTP, and Cisco's L2TP methods. In my Ubuntu system, I use apt-get, but you can also search for the appropriate plugins with Synaptic. Once you've added the plugin, all you have to do is click on the network icon then select VPN connections to begin entering the appropriate information. Figure 5 shows the steps for configuring a Cisco connection on an Ubuntu system.
NetworkManager supports both shared-key and X.509 certificate-based encryption. The keys to getting NetworkManager to function properly include installing the racoon daemon software to handle the Internet Key Exchange, creating or otherwise obtaining a shared key from your administrator, and creating or otherwise obtaining signed certificates from your administrator (if you are using certificates). Also, you have the option of importing the saved configuration files of existing connections.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs