Exploring Samba's new registry-based configuration
Registry Configuration in the Cluster
A cluster setup faces the inherent chicken and egg problem: The registry is stored in the registry.tdb database, and CTDB has to distribute it across the cluster. To enable distribution of the registry, the administrator initially needs to configure Samba with the clustering = yes option set before registry globals are read. So unfortunately, the registry-only configuration with config backend = registry is not an option here. Instead, the admin should copy the minimal smb.conf file in Listing 2 as a default configuration to all cluster nodes once. Afterwards, the whole Samba cluster can be configured centrally through the registry.
Accessing Registry Configuration Data
Samba provides several approaches for editing the registry. Before you can modify the Samba registry, you need to enable remote access for your designated management account using the following command:
net rpc rights grant user SeDiskOperatorPrivilege
regedit.exe
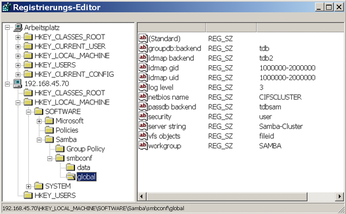
Because the registry is available remotely over the WINREG RPC interface when the Samba daemon smbd is running, the most obvious method of access is through the Windows registry editor regedit.exe (Figure 2).
The advantage of the registry editor is that it gives the Windows admin the opportunity to configure a samba server with familiar tools. But in the long run, this method will probably be too awkward, even for hard-core Windows addicts.
« Previous 1 2 3 4 Next »
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs