Tools to prevent drive-by attacks
The Client Approach
After you have secured your own web service against the injection of malware and exploit kits, the next task is to protect your clients on the network. To measure the extent of potential security problems, you first need an inventory of the browser plugins and any other Internet software. Client management systems, such as ACMP (Aagon) OPSI (UIB), Altiris (Symantec), or Empirum (Matrix42), have appropriate inventory modules that help accurately record and evaluate the software used along with software versions. These tools will help you develop and roll out a patch management policy for the affected applications without user intervention.
Another group of browser-checking tools is focused on home users or administrators who only have to manage a few computers. For example, the Anti-Botnet Advisory Center, also an initiative of the Internet industry association, eco, offers a review of the browser and the installed plugin versions. If the browser check finds outdated plugins, you can update by clicking a button. Unfortunately, this solution only really works reliably for popular plugins like Java and Flash. If you use specific plugins, such as the Citrix Receiver, you still need to take care of the update manually.
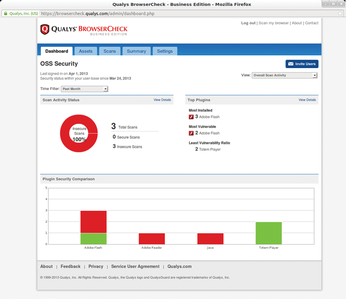
The same applies to the rather simplistic Check Your Plugins service by Mozilla [19]. The Qualys BrowserCheck [20] (Figure 3) does a better job, offering to install its own plugin optionally for a more intensive investigation. If this plugin is installed, it doesn't just identify most plugins reliably, it also offers advanced scanning methods – at least for Windows. You can check your current browser, as well as other installed browsers, and check the operating system security settings and the status of Microsoft patches. Qualys Business Edition – a version of the browser check for administrators – is also free. After registration [21], you can download an MSI version of the browser check plugin in the Settings section of the dashboard, which can be used to feed the plugin to Windows PCs from a central location. Alternatively, you can use a download URL for the plugin and a Quick Scan URL. The results of the scans are not sent to the user but displayed directly on the administrator's dashboard.
Automated Updates
Antivirus vendor F-Secure takes a different approach with its new software updater. Customers who already use the F-Secure Cloud Solution Protection Service for Businesses (PSB) [22] to manage their corporate systems can now deploy the software updater to manage computers along with the antivirus client from a central location, ensuring that no outdated browsers and plugins are used. The list of supported software [23] is quite impressive – in addition to the usual suspects, such as Java, you will find candidates like Foxit Reader and the VLC media player.
BLADE (Block All Drive-by Download Exploits) is a project in the making that was created with the support of the US National Science Foundation, the U.S. Army Research Office, and the Office of Naval Research (Figure 4). BLADE consists of a series of Windows kernel extensions to prevent hidden binary installations during a drive-by attack.
BLADE is being tested by the initiators with the most common browsers and daily emerging malware links; some zero-day attacks have apparently also been used in the past six months. According to the testers, BLADE has so far blocked 100 percent of the attacks, at least according to the results of evaluation lab, which are published regularly [24]. BLADE is not yet available, but in the next phase, a free version will be available for download.
HTML5 and NoScript
Browser extensions like NoScript or Flashblock can help prevent drive-by attacks. However, these plugins are of no benefit if they are installed in an outdated browser. Additionally, the don't really attempt to find any malicious code but simply disable features such as JavaScript or Flash. Because many sites are practically unusable without JavaScript, these tools are therefore probably more suitable for IT professionals. The upcoming HTML5 standard will certainly contribute to greater safety because plugins such as Flash are no longer required for displaying video, thus reducing the number of products with software vulnerabilities.
Another approach to client protection is not to use locally installed browsers or other Internet software. Instead, the browser is launched in an enclosed environment, like a virtual machine. As an alternative, you can use a Live medium (e.g., a Linux Live DVD or a USB flash drive) and run the browser installed there. One reason not to use Live media, of course, is the overhead of the necessary reboot and the quick obsolescence of browsers on Live CDs. Sirrix [25] offers Browser in the Box, a solution in which the browser is launched in a local VirtualBox VM. The VM is based on a hardened Debian 6 Linux with SELinux and the current Firefox browser. The single-user version is available for download free of charge; the enterprise version is only supplied in combination with a web gateway and a management system.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.