Exploring the openATTIC unified storage manager
Managing Volumes and Grabbing Snapshots
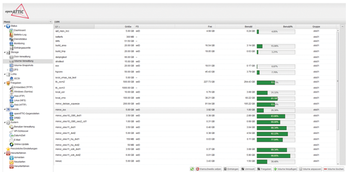
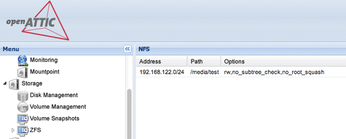
The Volume Management screen (Figure 2) oversees storage volumes and other resources: If you want the openATTIC machine to use a volume for a specific purpose, such as an NFS export (Figure 3) or a Samba share, you first need to create the volume. In the same menu, you will find the snapshot function, which lets you create snapshots of storage devices and volumes. A special treat: OpenATTIC also supports ZFS. If you rely on iSCSI in your network, you can also use the web interface to create iSCSI LUNs, which you can then integrate as local disks on the target servers.
In a mature IT setup, access to storage is desired not only at block level, but also via the various network file protocols, such as NFS or Samba. Often these network file protocols and services are distributed across various servers on the network and not centrally manageable.
Although openATTIC promises to put an end to this chaos, it succeeds only in part: The environment actually installs all the necessary components, such as NFS, FTP, and Samba server, and you can manage all these tools wonderfully via the Shares web interface menu. A previously created volume, for example, which is available as a local disk, can thus be shared quickly through NFS.
The same applies to Samba shares. If the admin has performed the appropriate steps in the web interface, setting up a Samba share for access by a Windows client is easy.
In view of these features, the quality of openATTIC is very impressive; in the lab, I really were able to create and use all the volumes as promised. On the other hand, openATTIC is deficient in situations where additional complex configuration is required; for example, the web interface still has no way to support Samba talking to LDAP.
System Management and HA
The fact that openATTIC is not only for storage management is clearly evidenced by the additional features available in the web interface. In essence, openATTIC is nearly comprehensive as a tool for system administration. For example, you can edit the system's network interface cards via the web interface. In Online Update, openATTIC provides a graphical update manager that calls Aptitude in the background. OpenATTIC automatically discovers which packages are upgradable on a regular basis; you only need to trigger this action.
The developers have also considered one other essential requirement of storage systems: high availability. In openATTIC, you can implement HA via the Peers function: For a full HA configuration, you initially need to build two openATTIC systems, each with its own API key. In the web interface, below Peers, you can then connect the two entities. If the openattic-module-drbd package is installed, you can proceed to set up replication.
If successful, openATTIC with Distributed Replicated Block Device (DRBD) ensures that the individual openATTIC machines always keep their data in sync. The nasty thing is that the mandatory set of HA programs, comprising Pacemaker and Corosync, cannot be configured via the web interface in openATTIC, but requires the use of additional software such as the Linux Cluster Management Console (LCMC) [4].
Given the fact that the implementation of a comprehensive GUI for Linux HA is extremely complicated, it is forgivable for openATTIC not to offer this feature at this early stage. It would be preferable for openATTIC to automatically integrate DRBD into an existing cluster manager.
Roller Coaster
OpenATTIC is promising, but in its current state, it still runs admins through a roller coaster of emotions. On one hand, the goal of providing a management front end for various storage technologies to put an end to the storage jungle is actually quite successful. After the installation, the environment is a complete management suite for any type of storage; it thus reduces the hassle of working with the many different protocols.
The fact that several openATTIC instances can connect with each other via the free API, and can also be incorporated into a high availability solution, is quite impressive. However, the installation is difficult, and an obscure shell script does not inspire confidence; to make matters worse, openATTIC currently only works reliably on Debian Wheezy.
Most likely, the choice of distribution is largely due to the personal preferences of the openATTIC developers. According to statements by Steffen Rieger, who manages openATTIC development at IT Novum, Wheezy really is the recommended distribution. But therein lies the rub: The market position that openATTIC currently adopts is not very meaningful. SUSE and Red Hat each have their own storage appliances that offer feature sets similar to openATTIC. If the project wants to compete with these solutions, it is inexcusable not to have pre-built packages for all enterprise distributions. But, if openATTIC wants to be an independent storage appliance that can be installed from a CD, the question arises as to why the project does not provide a matching image.
The openATTIC storage solution is fantastic and offers many benefits. But, unless it adds an Enterprise finish, the project will remain hidden to the many decision makers focused on enterprise-readiness.
Infos
- openATTIC: http://www.open-attic.org/en/home.html
- IT Novum: http://www.it-novum.com/en/home.html
- openATTIC documentation: http://www.open-attic.org/en/community/doku.html
- Linux Cluster Management Console: http://lcmc.sourceforge.net/
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs