Secure communication on the Internet with Whonix
Workstation
Use the Whonix workstation for anonymous surfing of the Internet. After booting, the system – like the gateway – will start the whonixcheck program to check system parameters. For whonixcheck to complete successfully, the Whonix gateway must be active, because the workstation uses its isolated network to access the Internet. Without a properly working gateway, Whonixcheck exits with an error message.
Like the gateway, the workstation also comes with KDE desktop version 4.14.2 configured for the US keyboard layout. The following steps are already known: Go to System Settings | Input Devices to enable your choice of keyboard layout if needed, then type
sudo apt-get dist-upgrade
to install all the pending updates.
Next, click on the Tor Browser (AnonDist) desktop icon. Whonix opens a dialog for the cryptographically verified installation of the Tor browser: It is missing on the VM because of the fast update cycles. The script always gives you the latest version of the browser; the routine lets you select from multiple versions. The Tor browser is downloaded via the Tor network, which is much slower than using a direct connection (Figure 6).
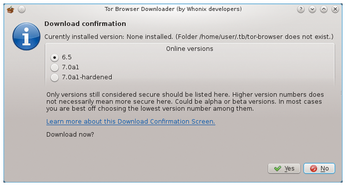 Figure 6: The Whonix workstation loading the Tor browser off the web for the first time and installing it automatically.
Figure 6: The Whonix workstation loading the Tor browser off the web for the first time and installing it automatically.
During the session, you can trace the entire data transfer very conveniently on the Whonix gateway. You can call monitoring by clicking on Arm - Tor Controller. A straightforward ncurses screen displays the transfer rates, as well as various statistical data for the active Internet connection and system resources (Figure 7).
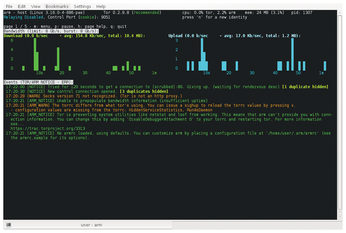 Figure 7: The Whonix gateway monitor clearly shows what is happening on the line tunneled through Tor.
Figure 7: The Whonix gateway monitor clearly shows what is happening on the line tunneled through Tor.
Test
After installing the Tor browser, the Tor Browser (AnonDist) icon is now ready for use on the desktop; otherwise, only two launchers for chat applications can be found on the desktop. Even the submenus lack the usual applications and only show you the software for online applications, such as video and audio players or a PDF viewer.
To verify the security of your Internet access, enter http://www.ip-check.info in the Tor browser address bar. After a detailed examination of the connection parameters, you will see a list of components relevant to safety (Figure 8). To avoid the kind of insecure technologies that websites tend to use, the Tor browser uses the NoScript and HTTPS Everywhere extensions, which stop scripts and unencrypted connections.
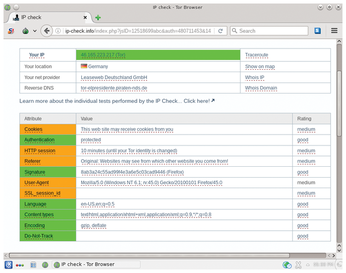 Figure 8: More or less all systems are go! Whonix has succeeded in keeping the system from revealing too much about the user.
Figure 8: More or less all systems are go! Whonix has succeeded in keeping the system from revealing too much about the user.
Conclusions
You can achieve a high degree of anonymity on the Internet by deploying Whonix on conventional Linux systems. Unlike special external solutions, such as hardened distributions on USB flash drives that only work in read-only mode, Whonix is also suitable for machines running from a hard drive, saving the user the trouble of booting to change to the secure system. Whonix is fully isolated from the host PC so that no data exchange can take place between the Whonix VM and the host – whether wanted or unwanted.
The Whonix developers always keep the Debian derivative up to date. Tough hardware requirements, thanks to VirtualBox, and having to run two VMs are the only shortcomings. For a smooth experience, the computer should have a reasonably recent processor and enough RAM and disk space. If these conditions are fulfilled, Whonix is one of the best ways of establishing an anonymous Internet connection at any time.
Infos
- Whonix for VirtualBox: https://www.whonix.org/wiki/VirtualBox
- VirtualBox download: https://www.virtualbox.org/wiki/Linux_Downloads
- Whonix for KVM: https://www.whonix.org/wiki/KVM#Landing
- Verifying the download: https://www.whonix.org/wiki/VirtualBox/Verify_the_virtual_machine_images_using_the_command_line
- Documentation: https://www.whonix.org/wiki/KVM#Why_Use_KVM_Over_VirtualBox.3F
« Previous 1 2 3
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs

