The next generation: Mozilla Firefox 3
Conclusions
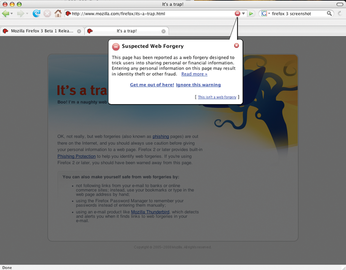
Firefox 3 made a good impression with new features, such as improved phishing protection (Figure 6) and easier installation of add-ons that do not originate from Mozilla's add-on page. The developers have introduced further improvements with Beta 4 [14]. Firefox 3 looks likely to have support for the Internet keys on multimedia keyboards and will have improved support for Gnome session management.
Overall, Firefox 3 is a critical component of the Linux desktop. In the future, the software will integrate almost seamlessly, at the same time adding a number of convenient functions. Users who prefer the KDE desktop will be disappointed – Firefox is yet another project that has decided in favor of Gtk.
Infos
- Firefox roadmap: http://wiki.mozilla.org/ReleaseRoadmap
- Firefox download: http://www.mozilla.com/en-US/firefox/all-beta.html
- Places system: http://wiki.mozilla.org/Places
- Places API: http://developer.mozilla.org/en/docs/Places
- Acid2 browser test: http://www.webstandards.org/action/acid2/
- Cairo (Wikipedia): http://en.wikipedia.org/wiki/Cairo_(graphics)#Mozilla
- Mozilla and Qt: https://bugzilla.mozilla.org/show_bug.cgi?id=297788
- Nightly builds: http://ftp.mozilla.org/pub/mozilla.org/firefox/nighly/latest-trunk/
- Firefox with Gtk pring dialog: http://ventorsblog.blogspot.com/2008/01/print-me-print-me-print-me-man-after.html
- CSS performance test: http://www.howtocreate.co.uk/csstest.html
- Load Time Analyzer: https://addons.mozilla.org/en-US/firefox/addon/3371
- Test table: http://howtocreate.co.uk/jslibs/oldindex.php
- JS performance test: http://webkit.org/perf/sunspider-0.9/sunspider.html
- Firefox Beta 4: http://ventnorsblog.blogspot.com/2008/02/beta-4-quickies.html
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.
-
ZorinOS 17.1 Released, Includes Improved Windows App Support
If you need or desire to run Windows applications on Linux, there's one distribution intent on making that easier for you and its new release further improves that feature.