Evaluate systemd logs using journalctl
Finding the Time
If necessary, you can filter logs to show events at exact times. This is very helpful for computers that are not restarted often. Use the options --since and --until to narrow down the time window to the minute or second as required. You can also combine these options.
You can see an example of using one of the options on its own in the first line of Listing 5. The second line contains an example of using both. If you are specifying the time, it must be in the format YYYY-MM-DD HH:MM:SS. You can also use more general options such as --since yesterday, as shown in Listing 5.
Listing 5
Filtering Logs by Time
Filter by component
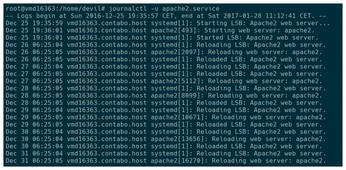
There are other filters you can use to search for specific events. This means you can detect messages relating to individual components. For example, if you are experiencing problems with your web server, use journalctl -u apache2.service to display only related events (Figure 3).
If you have an idea of where the error may be occurring within the web server, refine the filter further, as in the example query (Listing 6, line 1) of a suspect PHP module. To investigate specific processes, you can also filter by process, user or group ID.
Listing 6
Filtering by Component
First, look for the corresponding process ID. You can do this using the commands pidof or ps (Listing 6, lines 2 and 3). Next, query the corresponding process using the option _PID= (line 4). In Debian, you can find the user for the web server using the command id -u www-data (line 5), for instance to display all events since midnight (line 6). To display all possible filters, use man systemd.journal-fields.
You can also search for notifications from misbehaving applications. To do this, simply enter the relevant path. For applications installed via your package manager, these should be located in /usr/bin, for instance journalctl /usr/bin/amarok. For other apps, use which <name> to determine the exact path.
Including Kernel Messages
If your want to check for kernel messages, you can do so for the current session with journalctl -k. For information on previous sessions, use journalctl -k -b -n.
The option -p determines the priority of displayed messages. For instance, journalctl -p err shows error messages whereas journalctl -p crit displays critical messages. The log levels are the usual syslog log levels as documented in syslog(3) which you can find online, for instance on Wikipedia [4]. Both numeric and text values are accepted.
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs