Isolation with Qubes OS 4.0
First Impressions
After the initial setup is complete, you will find yourself in an environment that is reminiscent of Fedora. All controls are located in a bar at the top of the screen. First you launch the Qube Manager by clicking on the Q in the top right corner; the Qube Manager lists all the available domains. Each of the domains, or qubes if you prefer, opens a separate VM.
At the top, you see dom0. The dom0 domain is the domain in which the graphical user interface (GUI) runs without network access. You will want to update dom0 first (Figure 3). Below it are a few domains that start with sys, such as sys-net. These domains secure parts of the system. An attacker who gains access to the network card does not have access to other domains. Some template VMs follow. Fedora 26 is always available. Other templates for Debian 9 and Whonix depend on your choices during the install.
The Qube Manager also lists various App domains. In the default configuration, the domains are work, personal, vault, and untrusted.
To update a domain, select the entry and then click on the icon with the down arrow in the Qube Manager toolbar. The program loads all outstanding changes from the web and imports the corresponding packages into the VMs.
Next, update the template for Fedora 26. You don't have to worry about the individual personalized domains; just restart them after the Fedora template update completes. The domains are then automatically given access to the new packages.
Take a brief detour to Systemtools | Settings Manager and check the Mouse and Touchpad section if you want to use a touchpad. In the Panel section you can configure the bar at the top of the display or move it to another location.
Getting Cozy
After installing all updates, start setting up each workspace as needed. You can create new workspaces or clone existing workspaces (Figure 4). All this is done via the context menu of the individual domains. You can decide which application will run in which domain and what system resources are available (Figure 5).
 Figure 4: The main menu leads you to superordinate system tools and the settings for the individual VMs.
Figure 4: The main menu leads you to superordinate system tools and the settings for the individual VMs.
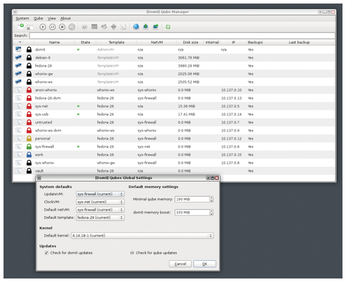 Figure 5: You can call both the global and the VM-specific settings from the context menu. Use the Settings dialog to configure the kernel version, allocated memory, firewall, and default template.
Figure 5: You can call both the global and the VM-specific settings from the context menu. Use the Settings dialog to configure the kernel version, allocated memory, firewall, and default template.
Files created via the desktop, such as screenshots, end up in the dom0 file manager. These files are then "stuck" because the dom0 domain does not allow access to the Internet or external data carriers. To let these files out of jail, you need to use a script to move them to a suitable VM. The following command:
qvm-copy-to-vm source target
will move these files for you. In the future, the developers plan to implement routines that facilitate this action.
Due to its structure, Qubes is not the fastest system when starting applications and activating domains, but it offers everything you need for a normal working day with a browser, word processor, and office applications.
Remote Control
In order to integrate Qubes OS 4.0 with a large network, the system must be reliably managed and remotely controlled by system administrators. Qubes OS now comes with the Qubes Admin API [9] for supporting automation and scripting. The interface is based on the Qrexec [10] framework. You can also use the Admin API to assign specific rights for administrators via policies.
The Admin API lets you securely restore backups created with older (and no longer trusted) versions of Qubes. In response to the CPU security holes "Meltdown" and "Spectre," most VMs in Qubes 4.0 now run as Hardware Virtual Machines (HVM) [11]. Qubes virtually never resorts to the somewhat-simpler paravirtualized VMs (PVM) in the standard configuration [12].
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs