Ubuntu Sixpack
Ubuntu Sixpack
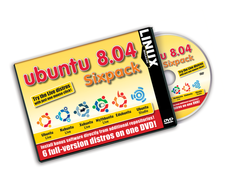
The arrival of Ubuntu 8.04 “Hardy Heron” signaled a new era for the whole family of distributions that use Ubuntu as a base. Kubuntu, Edubuntu, Mythbuntu, and other Ubuntu derivatives soon followed with new releases of their own projects.
The arrival of Ubuntu 8.04 "Hardy Heron" signaled a new era for the whole family of distributions that use Ubuntu as a base. Kubuntu, Edubuntu, Mythbuntu, and other Ubuntu derivatives soon followed with new releases of their own projects.
Sixpack
Rather than confining you to a single Ubuntu option, this month's Linux Magazine DVD offers several Ubuntu alternatives on a single disc. To browse for your favorite *buntu, simply insert this disc into your DVD drive and then reboot your computer.
Booting
If your system does not boot to the DVD, try changing the boot order in the BIOS configuration menu.
When your system starts, you'll see a boot menu (Figure 1). Select Try Ubuntu without any change to your computer and press Enter to confirm. The Ubuntu desktop will appear on your screen.
Virtual Machines
In the top left-hand corner of the Ubuntu desktop, you will see an additional Innotek VirtualBox icon that is not part of the standard desktop. Despite the padlock icon, you can still access the underlying software.
To launch the VirtualBox virtual machine, press the icon. Double-clicking the icon launches the program. The first thing you see is the Control Center, where you can manage individual virtual machines. The lower part of the window contains a list of pre-configured systems, including entries for Kubuntu 8.04 KDE 4, Mythbuntu 8.04, and Xubuntu 8.04. As the version number indicates, all three systems are based on packages for the latest version of Ubuntu.
To try one of the Ubuntu derivatives in a virtual machine, select an entry in the list and click Start. Ctrl+right arrow returns the host system to the foreground; however, the virtual machine keeps running. To return to a virtual machine, just click on the window.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

