Applying updates to an active kernel with Ksplice
Production Use
The current 0.8.6 version is available as a tarball with prebuilt binaries or as a source code archive under the GPLv2. Distribution packages do not exist as of this writing. If you build the tool from the source code, you will also need the BFD library, which you can retrieve on Debian or a derivative such as Ubuntu with the following command:
sudo aptitude install binutils-dev
Prominent developers, including Andi Kleen, have proposed adding Ksplice to the official kernel as an upstream extension. Kleen hopes this step would mean permanent support for the project, which would, in the long term, lead to an incremental compiler [4]. This would remove the need for developers to completely rebuild the kernel to test and modify patches.
The program itself consists of four Perl scripts that call a number of tools written in C to analyze the object code. ksplice-create only needs a path to the directory with the running kernel and details of the patch. One practical feature is that the administrator can specify a change in diff format with the --patch option or specify a file with the --diffext option in which the changes have already been completed. On top of this, the program needs a ksplice subdirectory in the kernel tree, where the administrator stores both the kernel configuration and the symbol table (see Figure 3).
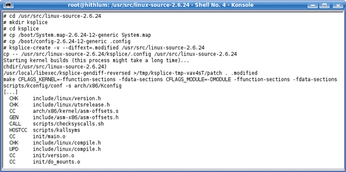 Figure 3: To prepare Ksplice, the administrator types ksplice-create in the kernel source directory and specifies the patch type. Ksplice then builds the old and new kernels and bundles the changes into an update module.
Figure 3: To prepare Ksplice, the administrator types ksplice-create in the kernel source directory and specifies the patch type. Ksplice then builds the old and new kernels and bundles the changes into an update module.
Depending on what kind of system you are using, the first phase can take a while because Ksplice needs to build two complete kernels: one in ksplice/pre and one in ksplice/post. After doing so, the program searches for differences and merges the results to create two kernel modules.
By calling ksplice-apply, you can apply the hotfix. The program first loads a module that takes care of trampoline management, then waits for the right moment. When the moment occurs, Ksplice loads the changes into the kernel, executes them, then removes itself to save memory.
Patch Management
Ksplice can also change a patched kernel. To do so, the patches from the first phase must reside in the source code's pre tree. ksplice-create and ksplice-apply take the trampolines into consideration and modify them correspondingly. The same mechanism makes it possible to undo changes by calling ksplice-undo because the system "remembers" the vector addresses. ksplice-view shows the changes performed by Ksplice.
On his website, Ksplice author Jeffrey Brian Arnold shows another potential application scenario for the tool: debugging the active kernel. If you just want to add a couple of printk() calls at various points to view data structures that are otherwise difficult to access, Ksplice gives you a simple approach to injecting them into a running system. However, this approach does not lend itself to more complex applications, for which dynamically loadable modules, Kprobes, or Systemtap are more useful.
Patented Approach?
Developers have pointed out that Microsoft posted a patent application with the US Patent Office (USPO) in December 2002 titled "Patching of In-Use Functions on a Running Computer System." USPO had refused the application, and Microsoft had appealed and posted a whole bunch of additional applications, including one for Efficient Patching (USPO reference 20050257208).
In response to this, half a dozen developers piped up in various forums pointing out that this technology was public knowledge on various platforms from PDP-11 through a state-of-the-art PC long before the software patent application was filed.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

