Features
Tutorials – Minetest
Building your own nodes and mods in Minetest
Minetest is much more than a clone of a certain popular proprietary game. It offers infinite customization that allows you to create blocks, objects, fun educational exercises, and even games within the game, dishing up features well beyond those of any other closed source alternative.
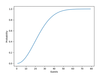
Programming Snapshot – Probability
Shared birthdays among party guests
At a party with 23 guests, having two guests with the same birthday in more than 50 percent of cases may sound fairly unlikely to amateur mathematicians. Armed with statistical methods, party animal Mike Schilli sets out to prove this claim.
Mermaid
Drawing on Command
Mermaid lets you create diagrams from simple text-based statements.
soundKonverter and fre:ac
Refound Sound
Transfer the contents of audio CDs to your PC and convert the contents of music folders with soundKonverter and fre:ac.
MakerSpace – Powerhouse
Raspberry Pi 3 Model B+ overview
The new Raspberry Pi 3 B+ stands out from its predecessor in many respects. Our tests show what the new model can do.
Gnome Recipes
À la Carte
Cutting recipes out of magazines and attaching them to the fridge is a thing of the past. Today, Gnome Recipes is your friendly kitchen helper.
Tutorial – USB/IP
Finders, Keepers
The Linux kernel has many interesting but unknown services. USB/IP, in particular, is one that you'll probably wonder why you have never encountered. USB/IP lets you use USB devices connected to other machines on your network as if they were plugged directly into your computer.
Programming Snapshot – Python Gambling
Strange Coincidence
Can 10 heads in a row really occur in a coin toss? Or, can the lucky numbers in the lottery be 1, 2, 3, 4, 5, 6? We investigate the law of large numbers.
Simply Secure
HTTPS out of the box with the Caddy secure web server
Caddy lets even the most inexperienced user set up a secure web server.
MPD and Cantata
Online Jukebox
The MPD server helps you manage your music collection flexibly and remotely and integrates external content.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.