Bitcoin Basics
Bitcoin Digital Currency
ByBitcoin is a decentralized virtual currency, popular with hackers and the open source community. We’ll explain how the money is created and how it works.
Although you probably don’t hear about bitcoin (a protocol for transmitting electronic money) and bitcoins (the unit of virtual currency) every day, the currency still exists. Apparently, enough people believe in bitcoin as real money to invest in it. In fact, in September 2012, bitcoin value spiked when a hacker who claimed to have access to US Presidential candidate Mitt Romney’s tax returns demanded a ransom of US$ 1 million to be paid in bitcoins.
Bitcoin Background
The decentralized electronic currency is based on an exciting idea and complex algorithms. During euro crisis times, risk-adverse investors without IT background are flirting with alternatives to euros, real estate, and gold. In addition to speculators and investors, regular folks are investing in bitcoins, attracted by its simple architecture: Smart algorithms replace a central authority exercised by a monetary monopoly. Instead of a central mint, users themselves create the virtual currency and distribute it using the P2P process, motivated by a clever incentive system. Overall, the model puts a sophisticated theory into practice.
If you want to get your feet wet with bitcoin, you need two essential things: willingness to take on risk and a lot of enthusiasm. The value of the Bitcoin currency fluctuates against the euro or dollar, and the conversion process is quite complicated. Additionally, you can’t exclude theft in the virtual realm. Security experts recently found a particularly egregious Trojan that installed a bitcoin miner to generate currency on a victim’s computer – with the unsuspecting user having to pay the price (see the “Bitcoin Mining” and “Bitcoin Clients” articles in this issue).
The frequent accusation that the anonymity of bitcoins makes them prone to illegal transactions and money laundering overlooks a fundamental point: All bitcoin transactions can be tracked online. They’re not so much anonymous as pseudonymous (Figure 1).
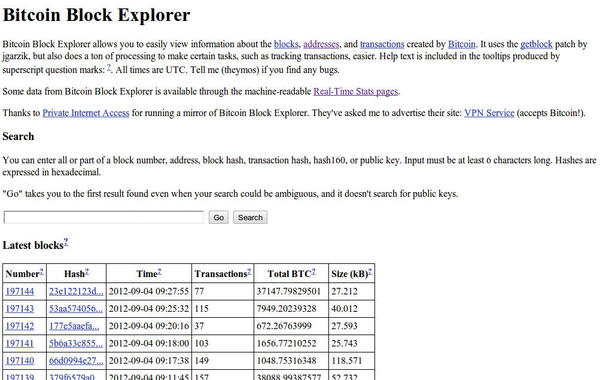 Figure 1: A website can trace bitcoin transactions way back, making cash comparatively more anonymous.
Figure 1: A website can trace bitcoin transactions way back, making cash comparatively more anonymous.
Finding a real person in the transaction chain can possibly lead to others. Regular cash is not only much more anonymous but also easier to use – if you put aside worldwide monetary transfers.
Making Money
How does bitcoin work? The problem with a functional digital currency is that it needs to meet various criteria. Currency senders and recipients must be identified unambiguously, and no fakes can be circulated. The currency cannot reproduce limitlessly – to reduce the risk of inflation. And, the virtual money must be easy to use in order to reach a critical mass in the community.
The inventor of the digital currency is a developer with the (presumed) pseudonym Satoshi Nakamoto. Some of the ideas in his original paper are indeed older – mainly the encryption piece – and are based on previous work by other researchers. Interesting is that some well-known kernel developers are also working on the bitcoin protocol and mining software, among them Jeff Garzik and Con Kolivas. Thus, the project has a strong link to the open source community; a growing number of open source developers are accepting donations in bitcoins, as evidenced on a recent website (Figure 2).
 Figure 2: Kernel developer Con Kolivas developed his own bitcoin miner and is accepting donations in bitcoins.
Figure 2: Kernel developer Con Kolivas developed his own bitcoin miner and is accepting donations in bitcoins.
The simple bitcoin trade is somewhat awkward, but not complicated. You don’t need to understand the concept behind the bitcoin trade, although it is interesting.
Buying and Selling
To buy and sell bitcoins, you must first visit one of the many bitcoin exchanges (e.g., bitcoin.de, mt.gox, and BitMarket.eu). Via a commercial bank transfer or direct debit, you can buy bitcoins accompanied by a secure account confirmation mechanism. The exchange then transfers a coin amount to your account and you must confirm the number in the comments. Bitcoins can also be traded locally from person to person, for example, in an Internet café (Figure 3).
No actual bitcoins exchange hands; rather, the other person sends money directly to your bitcoin address. A bitcoin client that you install on your computer can manage one or many of these addresses in its digital wallet. Bitcoin makers recommend a separate digital key per transaction.
Clients exist not only for Windows, Mac OS X, and Linux, but also for Android (Figure 4) and the iPhone. Bitcoin addresses are similar to email addresses, but are long, consisting of 34 alphanumeric characters.
This address makes you uniquely identifiable in the bitcoin network and ensures that your bitcoin transfer reaches its proper destination. Conversely, you can send amounts over the bitcoin client to the address specified by your counterpart. Still, be careful: Despite built-in autocorrection of bitcoin addresses, some transactions may end up in the ether if the address is valid but its owner doesn’t exist.
Technically, bitcoin addresses are nothing more than easily converted public keys, similar to when emails and files are encrypted. In a few steps, a program transforms the hash of the public portion of an ECDSA key pair into a bitcoin address. (ECDSA stands for Elliptic Curve Digital Signature Algorithm (DSA), a variation of DSA based on calculations of elliptical curves over finite space.)
The public key’s counterpart is the private key on your hard drive that your bitcoin wallet knows about. When someone sends you money, they use your public key. Authentication of the rightful beneficiary is through the corresponding private key that the bitcoin client knows from the so-called wallet file. If you want to take the virtual wallet, along with the bitcoin addresses, with you or secure it as a backup, you can load the wallet file on a USB stick, for example (see the “Which Wallet?” box).
After the bitcoin client starts, it loads or updates so-called block chains, which is part of the bitcoin security mechanism. Without block chains, the client can’t tell whether the stored bitcoins are actually valid, because block chains know about all previous transactions in the bitcoin network (Figure 5).
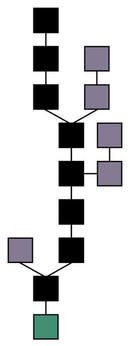 Figure 5: The block chain ensures that only valid bitcoins circulate by recognizing and including all transactions ever made (Theymos, CC-BY-3.0).
Figure 5: The block chain ensures that only valid bitcoins circulate by recognizing and including all transactions ever made (Theymos, CC-BY-3.0).
Mine Work
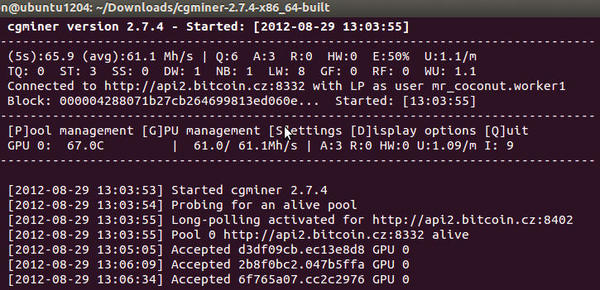
After the transfer, known in bitcoin parlance as a transaction, the bitcoin miner comes into play. The miner uses specialized software to prove whether the transaction is valid. The mining software (Figure 6) solves complex cryptographic tasks that the bitcoin network rewards on a regular basis with new bitcoins, thereby creating the digital currency.
The peer-to-peer (P2P) network behind the bitcoin system verifies each transmitter-receiver transaction. The transactions aren’t anonymous, but use a so-called “flooding” algorithm in the P2P network where the participating bitcoin miners collect them in blocks and digitally sign them (see the “Mining in Detail” box), providing computers with the ability to solve the cryptographic puzzle. The numerous miners have the job of decrypting these blocks. If decrypting is successful, the miner is then rewarded with 50 fresh bitcoins. Furthermore, the payer can (and should) pay a small amount, such as 0.01 or 0.005 bitcoins. The higher the fee, the faster the transaction in the bitcoin network. Once a recipient finds a valid block, the transaction fee also applies.
Whether or not a transaction is valid depends on how successfully some of the miners on the network insert the block with its various transactions into the block chain. A failure means that the transactions are unconfirmed and the bitcoins are voided.
Pool Party
At the time of writing, 50 bitcoins were equivalent to about 500 euros. You might think this conversion sounds good, but there is more than one catch. The likelihood of achieving this virtual treasure is intentionally set rather low. An algorithm randomly selects one of the world’s mining computers for a solution to the puzzle every 10 minutes. The probability of success also rests on the computer’s bitcoin mining processing capacity (measured in Mhash/s, which stands for million hashes per second and shows how the operations in the “Mining in Detail” box perform each second). This means that a supercomputer with 20,000 graphics cards has a lot better chance than a desktop PC with one graphics card.
Additionally, the bitcoin network permanently regulates the difficulty factor of the task, which is a great idea. This ensures that a block of 50 bitcoins is still awarded only every 10 minutes, despite increasing computing power. To get a block of 50 bitcoins on a single computer could take years, but, like winning the lottery, there’s always a chance of getting lucky.
Whereas the first miners could generate bitcoins with CPUs, today’s graphics processing units (GPUs) are being more generally deployed. Using special software (e.g., OpenCL), GPUs perform specific tasks much faster than conventional CPUs. To benefit from the computing power of GPUs, NVidia with CUDA and ATI/AMD with ATI Stream provide special interfaces that access OpenCL. During testing, the eight CPU threads of the computer could attain only two percent of the GPU’s performance.
Despite GPU support, a conventional computer could take years to decrypt a 50-bitcoin block. Thus, miners form syndicates in the form of pools. The more miners that join a pool, the greater the chance of one of them solving a bitcoin puzzle (Figure 7).
Pool operators then distribute the virtual money according to a certain key to all the miners in the pool, albeit in small but regular distributions. Participants with higher computing power get a better chance at the stakes. Because there are various distribution schemes, studying which of the mining pools is most suitable in advance is a good idea. Mining pool operators naturally keep part of the revenue for themselves, which helps finance the pool operation. Finally, mining pools undergo fluctuations: If more computers happen to solve cryptographic tasks on one day, there’ll be more money coming in than on other days.
Out of Bitcoin
Bitcoin mining is something like panning for gold; you can spend the entire day without finding a single nugget. At other times, you might strike it rich. Naturally, you can work out a probability factor for finding the meganugget, but there are no guarantees.
Unlike gold, where huge reserves can turn up unexpectedly, bitcoins are finite in number. In the end (in 2141) there are expected to be only 21 million bitcoins. Unlike traditional currency, bitcoins come in much smaller denominations; 0.00000001 (eight decimal places) is the smallest available denomination.
What happens next? Who checks the transactions when no more blocks of bitcoins pop out sometime in the future? In this case, transaction fees should make computing new blocks, transferred by bitcoin and going to miners, more attractive.
Risks
Some observers consider bitcoin “the most dangerous project we’ve ever seen,” which is a greatly exaggerated claim. Currently, the risk mainly falls to the users of the currency. For one thing, dragging someone to court for having retained bitcoins without coughing up the merchandise would still be rather difficult. On the other hand, you can cross over into difficult financial and political terrain by introducing bitcoins as an official currency. Still, the risks don’t faze bitcoin pioneers who expect bitcoins to replace cash within a legal framework.
Another consideration is energy consumption. Bitcoin makers are quick to point out the huge energy consumption of the big banks. Whether creating an alternative, independent monetary system justifies the energy savings is still a matter of debate.
So far, the total value of products purchased via bitcoin is only in the tens of millions of euros, and most people won’t swap out their credit cards for virtual money any time soon. Bitcoin is economically attractive for cost-effective, cross-border transactions, and bitcoin generation is exciting – but not so lucrative – for people with private computers. Powering computers costs more than generating bitcoins brings in, but this shouldn’t discourage enthusiasts. After all, the idea behind the virtual currency is fascinating, and there’s the fun factor of experimenting with mining software, mining rigs, and bitcoin clients.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Mint 22.3 Now Available with New Tools
Linux Mint 22.3 has been released with a pair of new tools for system admins and some pretty cool new features.
-
New Linux Malware Targets Cloud-Based Linux Installations
VoidLink, a new Linux malware, should be of real concern because of its stealth and customization.
-
Say Goodbye to Middle-Mouse Paste
Both Gnome and Firefox have proposed getting rid of a long-time favorite Linux feature.
-
Manjaro 26.0 Primary Desktop Environments Default to Wayland
If you want to stick with X.Org, you'll be limited to the desktop environments you can choose.
-
Mozilla Plans to AI-ify Firefox
With a new CEO in control, Mozilla is doubling down on a strategy of trust, all the while leaning into AI.
-
Gnome Says No to AI-Generated Extensions
If you're a developer wanting to create a new Gnome extension, you'd best set aside that AI code generator, because the extension team will have none of that.
-
Parrot OS Switches to KDE Plasma Desktop
Yet another distro is making the move to the KDE Plasma desktop.
-
TUXEDO Announces Gemini 17
TUXEDO Computers has released the fourth generation of its Gemini laptop with plenty of updates.
-
Two New Distros Adopt Enlightenment
MX Moksha and AV Linux 25 join ranks with Bodhi Linux and embrace the Enlightenment desktop.
-
Solus Linux 4.8 Removes Python 2
Solus Linux 4.8 has been released with the latest Linux kernel, updated desktops, and a key removal.