Finding Wireless Security Problems with Wifislax
Tracing
ByAlmost every wireless LAN has some potential security weaknesses. The Wifislax Slackware derivative helps detect and eliminate them.
Even before the revelations by Edward Snowden, security in computer communications was a hot topic, and it’s not just the spooks who are listening in: script kiddies, crackers, and war drivers can break into networks and do damage. Because WLANs are becoming increasingly popular, it’s not just PCs that connect wirelessly to one other; printers, TVs, and mass storage are all integrated in a WLAN.
Although Linux it is widely viewed as a bulwark against such machinations, the free operating system cannot prevent vulnerabilities in existing industry standards. Therefore, you should take a detailed look at the security settings of your wireless network and shut down any vulnerabilities. The Wifislax Live forensics distribution, which originates from Spain, reliably identifies weaknesses and helps you remove them.
First Start
The Wifislax ISO image, which weighs in at just 630MB, fits perfectly onto a CD. When launched, the system comes up with an unusual GRUB screen: You can then change the language setting to English in the first step and select whether to boot Wifislax with a conventional or PAE kernel. In a second splash screen, you can specify whether you prefer KDE SC or Xfce as your desktop environment.
Other startup options, such as loading the VESA video driver or disabling the ACPI settings, are used only for emergencies, if the operating system fails to launch with the desired options. After you have selected your preferred desktop, Wifislax boots into what at first glance appears to be an ordinary desktop (Figure 1).
An initial look at the various menus clearly shows that the distribution’s emphasis is on network security applications: You will not find the typical Linux programs like GIMP or LibreOffice or any multimedia applications. Additionally, frequently used Internet applications such as chat and email clients, BitTorrent, and news reader software are missing entirely.
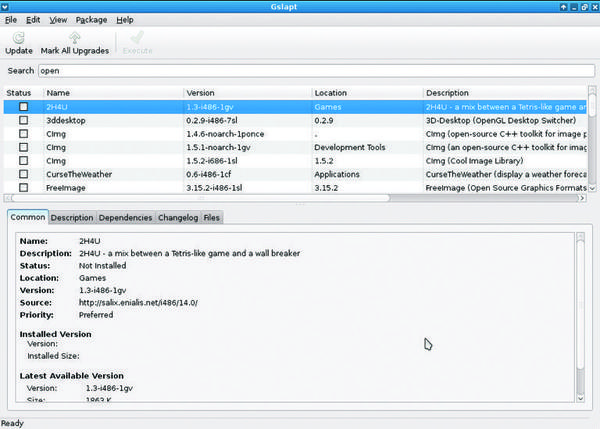
Only the System menu proves to be well provisioned straight out of the box; you also have the option of using the Install item to install the Wifislax operating system permanently. If you need additional software, Wifislax – as a Slackware derivative – offers Gslapt, a Synaptic-style interface as a front end that lets you to use the distribution’s software repositories. You can access Gslapt via the menu: System | Wifislax packets administrator | Packages admin with frontend gui (Figure 2).
Installation with Obstacles
Contrary to the assumption that Wifislax – like other well-known Linux distributions – can be installed on your hard disk with just a few clicks, the installation routine exhibits significant weaknesses in practice.
Although you use the System | Install Wifislax | Wifislax Installer QT to access an easy-to-use, graphical program for permanent installation, this tool will only be successful if you have previously prepared the hard drive with a third-party disk partitioning program.
The Wifislax installer fails to identify bootable partitions correctly when other Linux distributions already exist on the hard disk. Instead, the program proceeds to copy Wifislax to an imaginary new partition, which obviously fails. Because the installer is exclusively available in Spanish and has an unusual progress bar, as well, this process can quickly lead to confusion.
Partitioning the existing hard disk at the command line with fdisk or cfdisk is not sufficient. The hard disk can only be prepared successfully by calling System | GParted. Next, you must unmount all the active partitions on the storage medium and delete them. Then, you can create the new partition intended for permanent installation. The next step is to restart the system.
After booting, again call the installer. After it has finished its work, it offers to customize the GRUB boot manager. To do this, the routine relies on another external program. After installing GRUB 2 in the MBR of the disk, you can easily start the operating system. You now have the same software scope as in the Live version.
As a desktop environment, however, only the desktop previously selected in the Live mode is active; you are no longer required to choose between KDE and Xfce in the boot menu.
Network
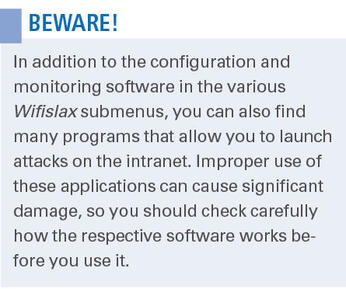
At the top of the main menu, you will find the Wifislax program group with various submenus. Here you will find all the applications you need to secure a wireless network. Among them are many virtually unknown programs; thus, it pays to take a closer look at the menus (but see the box “Beware!”).
The first step is to establish a connection between the Wifislax system and the WLAN. The Wifislax | Network Managers menu contains two well-known graphical tools: WiFi Radar and Wicd.
In the first tests with Wifislax, no wireless card was found, and thus no wireless networks, because my laptop has an older Intel wireless card with a Calexico2 chip that Wifislax – along with many other distributions – does not immediately support.
In this case, I first needed to obtain updated firmware for the WLAN chipset and then store the files with a suffix of .fw that I unzipped from the downloaded archive in the /lib/firmware/ directory. In contrast, two lab machines with wireless chipsets by Atheros had no problems and immediately cooperated with the ath5k and ath9k Linux drivers.
Tools
If you are interested in first gathering statistical and technical data for the WiFi network, you will find some familiar programs such as Wireshark, Zenmap, and Angry IP Scanner (in Wifislax | Network-Tools). Iptraf-ng and Net Activity Viewer are also found in this category.
Wifislax also comes with a considerable number of programs that support attacks on access points and client computers or that sniff passwords and access restrictions, usually achieved by using a variety of attack methods such as man-in-the-middle or dictionary attacks. Ettercap also is very powerful sniffing software, capable of sniffing passwords or logging traffic in switched networks.
Ghost Phisher is a no less safety-relevant program that allows you to offer spoofed services (DHCP, DNS, HTTP) via an imaginary access point. Ghost Phisher thus allows administrators to set up a honeypot to distract attackers from actual potential targets.
Applications that are not specifically designed for wireless networks, but also available in the Network-Tools menu, include CookieMonster (for editing cookies), Hydra (password cracker), or Hping (primarily for testing firewalls).
Wireless Security
To reveal the vulnerabilities of a wireless network reliably, Wifislax offers a plethora of programs that simulate attacks of various kinds in the Suite aircrack-ng and Wireless submenus of Wifislax. The individual programs in the Aircrack suite are command-line tools that accept a wide range of call parameters.
Wifislax simply opens a terminal and calls the appropriate program with the Help function, so you see the complete list of parameters in each case. Thanks to two scripts in the menu, you can use the program suite conveniently in a question-and-answer style, but this is only useful for users with knowledge of Spanish, because all the prompts are exclusively in the Spanish language.
Besides several programs for checking the security of networks protected by the WEP standard, the Wireless menu primarily contains software that supports the latest WPA and WPA2 specifications. Here, you can check whether the existing access restrictions in the form of passwords and keys are sufficiently secure (Figure 3).
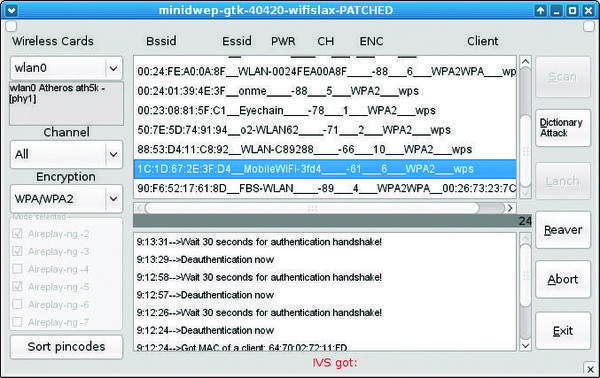
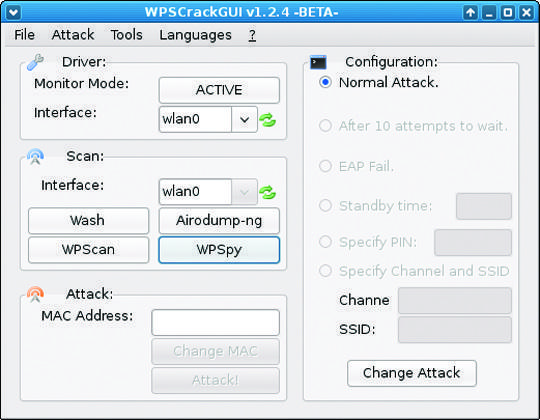
Wifislax also provides plenty of coverage for the relatively new WPS (WiFi Protected Setup) standard, which suffers from significant vulnerabilities. For example, it is no problem with PIN-based WPS authentication to decrypt the PIN within a few hours, like legacy WEP protection mechanisms. The attacker can recover not only the PIN number, but also the key used on the WLAN. This explains why the Wifislax developers have grouped various pieces of software for WPS testing (e.g., WPSCrackGUI in Figure 4) in the Wpa wps submenu.
In the Decrypters submenu, you will find some proprietary tools that rely on dictionary attacks to determine the access credentials of some routers, as configured by DSL providers. Because these scripts almost exclusively target providers headquartered in Spain and their equipment, their utility value is low in other countries.
Forensics
If you want to perform a detailed data analysis of the Internet use of a client computer, you can use the Dumpzilla tool provided especially for this purpose in the Forensics submenu. It extracts a full set of information from the logfiles of Firefox, Iceweasel, and SeaMonkey, including stored cookies, passwords, add-ons, downloads, and website history. Again, this program runs in a terminal, listing its comprehensive set of parameters in English.
Conclusions
Wifislax left a variety of impressions when compared directly with other security distributions.
On one hand, the system impresses with a very comprehensive range of security-related software that covers all the important areas of wireless communications. The WPS authentication software portfolio is extremely useful – and not yet available from other distributions, although WPS technology is spreading quickly. Another positive aspect is the good integration of terminal-based applications through custom scripts.
Less satisfactory, however, is the poor localization: Some scripts and applications exist exclusively in Spanish, and the system is not fully available in English. Additionally, the routine for installing Wifislax on disk has some significant weaknesses. That said, for network administrators who are looking to achieve clean wireless integration, Wifislax can be an extremely useful tool, despite its poor language support.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.