Root out rootkits
True Negatives
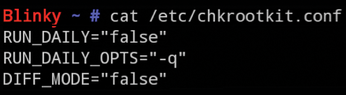
You can spend a moment disabling false positives by editing the /etc/chkrootkit.conf file. As you can see in Figure 2, you don't have many default config settings to worry about.
The first setting lets you choose to execute the Chkrootkit command on a daily basis. If that setting is changed from "false" to "true", you can peek inside the cronjob file /etc/cron.daily/chkrootkit to inspect the conditions used to launch the scheduled task. The RUN_DAILY_OPTS option tells Chkrootkit whether or not to produce output when a critical "INFECTED" status, or similar condition, is found. The "-q" here stands for "quiet."
If you wanted to receive the results of Chkrootkit tests every day by email, you could move the cron.daily/chkrootkit file somewhere like the /usr/local/etc/ directory and add the line in Listing 4 – or something similar – to your /etc/crontab or the root user's crontab. Note that if chkrootkit complains, you might need to adjust the beginning of the command by replacing the file name and its full path with cd /usr/local/etc; and then executing ./chkrootkit from within that directory. The example shown in the listing triggers every day at 1:00am. (Add your email address.)
Listing 4
Addition to crontab for Chkrootkit
To get rid of one of the Python false positives in Listing 2, you can add this entry to the foot of the /etc/cron.daily/chkrootkit file:
IGNORE="/usr/lib/pymodules/python2.7/.path"
After you've done that, try a test run to see if you're still getting false positives. Incidentally, if you want to peer into the innards of Chkrootkit, you'll find the -x option fascinating. Expert mode does put the onus entirely on the user to interpret the output, but it's very useful to run at least once. The -x option dutifully lists the suspicious entries that Chkrookit searches for inside the binaries it scans. To handle the large amount of output, you can read it as follows:
chkrootkit -x | less
If you only want to see which paths are checked, the manual helpfully offers this solution:
chkrootkit -x | egrep '^/'
You are also advised to mount a potentially infected drive to another machine so that you can inspect its content safely with the command:
chkrootkit -r /infected_disk-mountpoint
The chkrootkit package includes a few other tools that are also executed when the chkrootkit script runs. Among its other clever functionality, Chkrootkit will alert you as to whether your Network Interface Card (NIC) is set to listen in "Promiscuous Mode"; that is, your NIC is configured to listen for traffic that is not necessarily destined for your machine but is in fact visible on the network link to which it's connected.
Good, old network hubs were renowned for shouting loudly about everyone's traffic, but thankfully it's not as big a deal these days. Modern switched networks dutifully segment network traffic in a more secure fashion. However, you can achieve some interesting results from the ifpromisc tool included in the Chkrootkit package, even if your machine is connected to a switch.
Unless you know that a valid service (e.g., a network sniffer) has purposely configured your NIC to flaunt itself all over the network, you should probably be concerned if it is found to be running in Promiscuous Mode.
A malevolent attacker's modus operandi is to cover his tracks to avoid detection. One of the logging systems used on Unix-type systems resides in the wtmp (all logins and logouts) and lastlog (most recent logins) functionality.
With that in mind, you shouldn't be entirely surprised to hear that Chkrootkit also includes the chkwtmp and chklastlog tools to look for deleted entries in logfiles. Be warned that the manual makes an effort to remind you that all it can do is try to detect these altered logfiles and that these checks are far from foolproof.
Another piece of functionality that might be slightly alarming is the aliens test. This component apparently looks for any suspicious config files and network sniffer logfiles buried far, far away, deep into your filesystem.
Finally, the chkproc tool is used to separate the wheat from the chaff to identify unwelcome processes that might be running on your machine. It's a clever addition that checks what the ps command can see and then compares it to the /proc pseudo-filesystem entries, ringing a bell like a town crier if it finds something untoward.
End Of File
In this article, I have barely begun to look at rootkits. It's an ever-evolving subject involving the common cat and mouse chase between the good guys and the bad guys. Because you are now armed with new weaponry, I hope you can keep a closer eye on your machines. As you've seen, rootkits are very nasty trojan horse-style infections that can lie dormant for a relatively long period of time and then appear suddenly, biting you on the posterior.
Aside from knowing that your key system binaries are prone to compromise (and, as result, making you more aware of how important permissions and other security controls are), you should at least now be a little more familiar with the attack vectors that hackers consider. Admittedly, rootkit checkers won't save the day every time. If you do suffer a compromise, however, you'll probably know by the end of the same day that your machine has been infected and not several days or weeks later, when even more damage has been done.
For more information on Chkrootkit, the website encourages you to join its mailing list using
echo "subscribe users <email-address>" | mail majordomo@chkrootkit.org
and points you to some relevant books on the subject, as well [3].
Infos
- Chkrootkit: http://www.chkrootkit.org (accessed September 10, 2015)
- Source code: http://www.chkrootkit.org/download/
- Chkrootkit publications: http://www.chkrootkit.org/books
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.