User commands and logs
auth.log
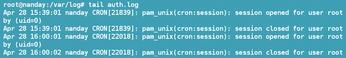
The log with the name auth.log records authorizations – that is, logons and logoffs on a system since the last time the system was booted (Figure 4). This information can be invaluable in checking patterns of usage and detecting any departures from the norm. Only the root user can view it.
user.log
user.log records the logins and logouts for the entire system, as well as any warnings that might indicate potential problems (Figure 5). In other words, this log is often a convenient point for troubleshooting general problems. As you might expect, only root can read this log.
User-Related Commands
Most commands have two types of options: Unix-like ones that are preceded by a single hyphen and are typically a single letter, and GNU options that are preceded by two hyphens and are usually a complete phrase that describes what they do. You can tell how old many of the user-related commands are by the fact that several of them have no GNU options whatsoever. In other words, when you are administering users, you are really getting down to the foundations of your operating system.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Red Hat Adds New Deployment Option for Enterprise Linux Platforms
Red Hat has re-imagined enterprise Linux for an AI future with Image Mode.
-
OSJH and LPI Release 2024 Open Source Pros Job Survey Results
See what open source professionals look for in a new role.
-
Proton 9.0-1 Released to Improve Gaming with Steam
The latest release of Proton 9 adds several improvements and fixes an issue that has been problematic for Linux users.
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.