User commands and logs
groups
As you might guess from the name, the groups command extracts selected information from the /etc/group file and displays it (Figure 9). With no options, groups lists information for the current user, but a valid username can be used as an option instead.
finger
For some reason, the finger command is not installed by default on the desktops of many distributions. However, if you are administering a multiuser system, it is well worth installing.
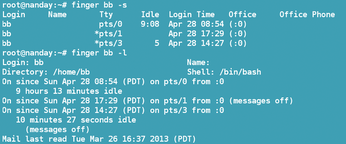
Without the use of any options, or with the -s option (Figure 10), finger followed by an account name lists the login name, the name, the interface, how long the user has been idle, when they logged in, their office, and their office phone number. If, like many home users, you leave the name, office, and office number blank when you create users, these columns will, of course, be empty.
Using the -l option, you get the same information reformatted, plus the user's home directory and login shell, as well as the last time they received internal mail. For administration work, this option is probably the most useful.
w
One of the most useful commands for gathering information about users, w, is also one of the simplest. It shows what processes a user is running at the time the command is run.
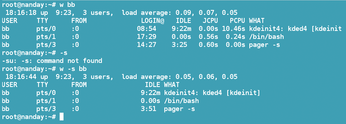
Entering the w command plus a username (or omitting a username and defaulting to the current account) produces a table of information for the user (Figure 11). From left to right, the information is the user account, its terminal, its remote host (0 if none exists), the login time, the length of idle time, the JCPU or time used by all processes attached to the terminal, the PCPU or time used by the current process, and the name of the current process.
If you choose, you can run a shorter summary by using the -l option. The information displayed using the -l option omits the login time, the JCPU, and PCPU.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
OSJH and LPI Release 2024 Open Source Pros Job Survey Results
See what open source professionals look for in a new role.
-
Proton 9.0-1 Released to Improve Gaming with Steam
The latest release of Proton 9 adds several improvements and fixes an issue that has been problematic for Linux users.
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.