Encrypting files and drives
Lock and Key

The security of personal data is a major topic in the Linux world. zuluCrypt gives users a tool for uncomplicated encryption of any data.
External data media are very popular. They allow you to back up large amounts of data quickly and easily, without spending a fortune on backup media. But, transportable hard disks or USB sticks can be easily lost or stolen because of their compact size and light weight. Therefore, you should never store your personal data on mass storage without protecting it with powerful encryption. With dm_crypt/cryptsetup and the zuluCrypt graphical interface, you can achieve this on Linux in next to no time.
Preparations
Under the free operating system, the standard method of data encryption is a combination of the dm_crypt kernel module and the cryptsetup command-line tool. You can use these to encrypt entire partitions and device files. The Linux Unified Key Setup (LUKS) extension contained in cryptsetup since version 1.0.5 also unifies the file format and allows the use of multiple keys. LUKS expands the encrypted data, adding a 592-byte header that stores the metadata and up to eight keys [1].
Almost all distributions have had cryptsetup in their repositories for some time now, so it can easily be set up using the respective package manager. In contrast, zuluCrypt usually requires a manual install because so far only a few distributions include it in their software collections. Only Arch Linux and PCLinuxOS provide packages for zuluCrypt; Mageia can use the packages from PCLinuxOS.
If you are using a different distribution, download the source tarball for zuluCrypt down from the project site [2]. After unpacking the archive with the command tar xjvf zulucrypt-4.6.2.tar.bz2, change to the newly created subdirectory. Be sure to read the BUILD_INSTRUCTIONS file and follow the instructions for installing the software: ZuluCrypt has a large number of dependencies that must be installed correctly for the program to work properly.
Integrating the PCLinuxOS packages in Mageia is not a smooth process: To satisfy the dependencies – so that the package manager can even install the main package on your disk – you first need to retrieve and install the secondary packages: libcryptsetup, libpwquality, and libZulucrypt [3]. After that, Zulucrypt will install without complaint and create a Zulucrypt in Gnome below the Applications | Tools | System Tools subdirectory; in KDE, you will find the software in the Tools | Configuration.
Systematic
Before you start to use the intuitive program interface to encrypt drives, you will want to visit the zuluCrypt wiki [4] to check up on the recommendations for dealing with different types of partitions. ZuluCrypt distinguishes between system and non-system partitions, and accidental encryption of a system partition can have unforeseen consequences.
For zuluCrypt, all drives in the /etc/fstab file are system partitions. Usually, they will include the actual system volume, the swap partition, and partitions on which user-defined data are stored. In contrast, removable disks do not appear here; zuluCrypt considers them to be non-system partitions.
Getting Started
After it is launched, zuluCrypt comes up with a very simple interface: The program window offers just a menu bar and the table columns Encrypted volume path, Encrypted volume mount point path, and Type.
To begin, you need to create a container in which to store the encrypted files. This container is then assigned a random key. The key should be as complex as possible and consist of uppercase and lowercase letters and numbers in mixed order; this makes it immune to attempted unauthorized decryption using dictionary and brute-force attacks.
Please note that decryption of the container relies on your entering the correct key. If you forget this, or it cannot be reconstructed for other reasons, the stored data are lost. Therefore, zuluCrypt also offers the option of first generating a keyfile that it uses not only to create a container but also to simplify decryption.
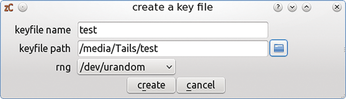
You can generate a keyfile using the Create menu, Keyfile feature; you need to specify the file path and the name of the keyfile. For security reasons, you should not put the keyfile in your home directory, but on an external disk if possible; this makes decrypting the container without the external storage medium containing the keyfile impossible (Figure 1).
In the next step, you can now create the container file. It appears later in the file manager as a conventional mounted drive. Before installing a container, you should check whether the destination drive is mounted. You can do this at the command line with the mount command without entering parameters. If the target drive is mounted, remove it from the list of active volumes with the umount <drive> command; zuluCrypt cannot process mounted drives.
Then, open the Create menu to generate the container. Here you have a choice between the options encrypted container in a file and encrypted container in a partition. If you want to encrypt large amounts of data, the option to place the container in a partition is recommended. Before you create the container, however, note that it fills the entire selected partition and you will lose any data that it previously contained.
In the next step, zuluCrypt indicates the possible partitions for creating the container; it does not display any system partitions by default. External drives are listed both by device name and by the associated UUID. If you will frequently be using removable media like USB sticks, external hard drives, or memory cards and accessing the encrypted container on multiple computers, you will want to select Use uuid when creating the encrypted volume. ZuluCrypt then identifies the container by its UUID in the future. This step prevents confusion when using several external drives simultaneously on a computer.
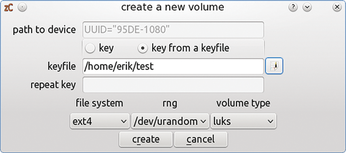
After double-clicking the desired drive, you need to associate the key with the container. If you have already created a keyfile, you can use this by pressing key from a keyfile. Next, specify the path to the keyfile in the input line below. Fortunately, this step also saves you from repeatedly entering the key for verification like in the manual create process.
In the lower part of the window where you create the container, you still need to define the filesystem and the encryption type. The default option in zuluCrypt is luks; this generates a 256-bit symmetric key in line with the Advanced Encryption Standard (AES). Pressing the Create button finishes creating the container (Figure 2).
ZuluCrypt then urgently prompts you to back up the LUKS header. The LUKS header stores various metadata such as information about the container as well as different keys, so a backup is very much recommended. ZuluCrypt opens the already familiar file dialog; by default, it offers to store the backup on the encrypted volume for safety reasons, but in your home directory. However, you can back up or – if the original header is destroyed – restore the LUKS header at any time in the zuluCrypt program window via the luks | backup header menu.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.