USB flash drives with Live Lernstick distro deliver educational software in schools
With just a USB stick and a portable hard drive or SD card, teachers of primary through secondary courses can provide their students a consistent learning experience, in and out of the classroom. The Lernstick (learning stick) distribution [1] is a slightly modified Debian 7 Live system with numerous educational programs aimed at different ages, including the 3D Marble Virtual Globe, the computer game TuxMath, a vocabulary trainer named Parley, and the music notation program Reunion (Figure 1).
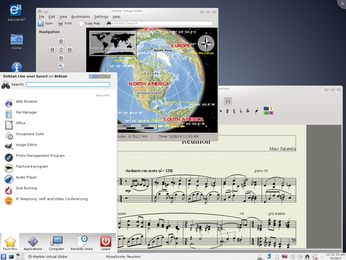 Figure 1: Lernstick comes with numerous well-known programs from a variety of disciplines, including the music notation software Reunion.
Figure 1: Lernstick comes with numerous well-known programs from a variety of disciplines, including the music notation software Reunion.
School Days
A lack of education funding means that schools are rarely able to provide their students with computers. Instead of sending parent teacher associations begging, the students could bring their own laptops to classes. This also offers the advantage of being able to continue working at home with the same device.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
UN Creates Open Source Portal
In a quest to strengthen open source collaboration, the United Nations Office of Information and Communications Technology has created a new portal.
-
Latest Linux Kernel RC Contains Changes Galore
Linux kernel 7.0-rc3 includes more changes than have been made in a single release in recent history.
-
Nitrux 6.0 Now Ready to Rock Your World
The latest iteration of the Debian-based distribution includes all kinds of newness.
-
Linux Foundation Reports that Open Source Delivers Better ROI
In a report that may surprise no one in the Linux community, the Linux Foundation found that businesses are finding a 5X return on investment with open source software.
-
Keep Android Open
Google has announced that, soon, anyone looking to develop Android apps will have to first register centrally with Google.
-
Kernel 7.0 Now in Testing
Linus Torvalds has announced the first Release Candidate (RC) for the 7.x kernel is available for those who want to test it.
-
Introducing matrixOS, an Immutable Gentoo-Based Linux Distro
It was only a matter of time before a developer decided one of the most challenging Linux distributions needed to be immutable.
-
Chaos Comes to KDE in KaOS
KaOS devs are making a major change to the distribution, and it all comes down to one system.
-
New Linux Botnet Discovered
The SSHStalker botnet uses IRC C2 to control systems via legacy Linux kernel exploits.
-
The Next Linux Kernel Turns 7.0
Linus Torvalds has announced that after Linux kernel 6.19, we'll finally reach the 7.0 iteration stage.
