Isolation with Qubes OS 4.0
Safe Cube

By isolating complete work environments in virtual machines, Qubes OS offers a significant security boost.
Linux users with an eye on security often turn to Live systems such as Tails [1]. One significant limitation of the leading security distros is that they offer little protection at runtime: All applications run in a common context.
Qubes OS [2] takes a different approach. Security in Qubes is the result of isolation. Chief developer and security researcher Joanna Rutkowska [3] assumes that, with the millions of lines of code and instructions in today's applications, no perfectly error-free desktop user environment can exist. She calls Qubes OS a "reasonably secure operating system."
Isolation has been an option within the Linux scene for years. Technologies such as sandboxes, containers, and virtual machines (VMs) all offer some means to limit an application's access to the system. If isolation is deployed effectively, an intruder who takes over the application won't be able to access the rest of the operating system. Qubes OS is designed with the goal of building this isolation into the user environment, so it is extremely easy to implement. In fact, there is no excuse not to implement it.
In 2007, Rutkowska founded security corporation Invisible Things Lab [4] in Warsaw, which specializes in security research. Since 2010, the Invisible Things team has also been developing Qubes OS. Version 4.0 is now available after almost two years of development. The latest update includes many changes. The system is based on Fedora with Xfce as the desktop environment, kernel 4.14.18, and the Xen 4.8 hypervisor to enable mutual isolation of workspaces or applications on separate VMs.
Cubed
In Qubes OS, isolation units are known as qubes. You can set up one qube for insecure websites and another for banking transactions, each with different authorizations. If the qube for insecure websites is compromised by malware, the attacker is still denied access to the qube for banking transactions.
The developers ensure this protection by giving the qube read-only access to the filesystem of the VM template on which it is based, so that a qube cannot modify a template in any way. In addition, Qubes offers the option to create "disposable VMs." A disposable qube could be used to open email attachments or suspicious files and dispose of the VM afterwards.
Qubes also encapsulates the network and storage subsystems into separate domains, as VMs are known in Xen. The different domains are based on VM templates that control the rights of the domain and provide the basic framework. A minimal host system with the Xfce desktop runs on the privileged admin VM dom0. In addition to other changes (see the box entitled "Qubes OS 4.0"), Qubes OS 4.0 significantly expands the system of domains.
Qubes OS 4.0
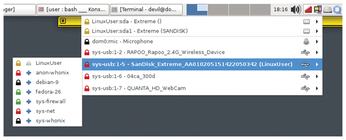
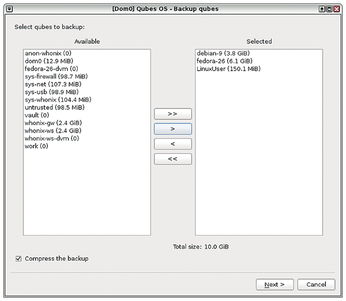
One of the goals of the Qubes 4.0 cycle is to replace the Qube Manager management tool with standalone tools that replicate most of its original functionality. Qube Manager offers a graphical approach to starting and stopping VMs. In version 4.0, USB sticks, mice, headphones, microphones, and similar devices can now be assigned to or removed from a VM using an icon top-right in the panel (Figure 1). Also, unlike the previous version, the system now encrypts all backups (Figure 2). See the release notes for a summary of other changes with Qubes OS 4.0 [5].
Hardware Diva
Due to its structure, Qubes could easily be called demanding when it comes to system resources. The hardware must have a 64-bit Intel or AMD CPU that supports Intel VT-x [6], VT-d, and Extended Page Table (EPT) or AMD-V [7], AMD-Vi, and Rapid Virtualization Indexing (RVI) virtualization technologies. In addition, you'll need at least 4GB RAM and 32GB free hard disk space.
Not only must the CPU support the necessary virtualization features; these features must also be enabled in the BIOS/UEFI. To find out more about your hardware configuration, use the command:
sudo cat /proc/cpuinfo
Check out the Qubes documentation for a list of compatible devices [8]. Typically, some ThinkPads and the current models by Tuxedo Computers are well-equipped for Qubes.
You can test the compatibility of your computer with Qubes OS by simply starting the installer. Qubes does not start as a live system due to its functionality, but the wizard checks the hardware for its suitability while the installation routine is loading. At the beginning of the installation process, after selecting the language, you might see a warning about virtualization functions that are missing or disabled on your hardware.
In particular, don't ignore the warning about the lack of support for IOMMU, also known as VT-d on Intel processors, and Second Level Address Translation (SLAT), also known as hardware storage virtualization. The installation can continue in these cases, but the system will not function fully as intended.
If IOMMU is not supported, you can work around the problem by downgrading the virtualization mode for the sys-net and sys-usb VMs from HVM (Hardware VM) to PV (ParaVirtualized). To downgrade the virtualization mode, run the commands from Listing 1 with administrative rights in the dom0 terminal.
Listing 1
Downgrading the Mode
Read First
Qubes OS uses Fedora's Anaconda installation wizard. If you are not familiar with Anaconda, you might have a hard time with the partitioning step at the beginning, but after a little trial and error, you will soon understand the underlying system. By default, the system encrypts the data carriers completely, but you can disable this option.
Before you get started, it is a good idea to browse the well-designed documentation. The installation itself takes about half an hour on state-of-the-art hardware; after the usual reboot, the initial setup follows. As a newcomer, you will want to accept the default settings. If you selected Whonix at the beginning of the installation, you should enable it here. The setup takes another 10 minutes.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.