Fixing Disks with Parted Magic
Disk Aid
ByIt’s really annoying when a disk suddenly dies on you or a typo in a command deletes important data. The free Parted Magic Live distro offers help.
The explosion of hard disk capacities in recent years, coupled with the ever-improving multimedia capabilities of conventional computer systems, has led to massive growth in volumes of data in many households. But HD video, lossless audio files, and elaborate games force you pay more attention to backing up your data. Many naive users invest in expensive, commercial software, often accompanied by a yearly subscription fee, to create backups of their mass storage.
However, the Parted Magic Live distribution gives you a permanent answer to backup problems. Parted Magic bills itself as “a complete hard disk management solution.” The Live system comes with a collection of useful tools for partitioning, backup, disk cloning, data rescue, and more. Although the maintainer has recently asked for a contribution to help finance the GPL-licensed distribution, the price of just under US$ 5 is something anyone can afford.
Variants
Parted Magic offers several start options in the GRUB boot manager. If you use the operating system on an older machine with only 512MB of RAM, choose the Start option Live with default settings 32 (for 32-bit machines) or Live with default settings 64 (for 64-bit PCs).
For more recent computer systems with more memory, opt for the Default settings 32 or Default settings 64 instead. This loads the entire operating system into memory and thereby accelerates the process enormously. If you see a black screen after startup, you can use Alternate graphical server 32 or Alternate graphical server 64, which load a VESA-compliant graphics driver and invoke a shell.
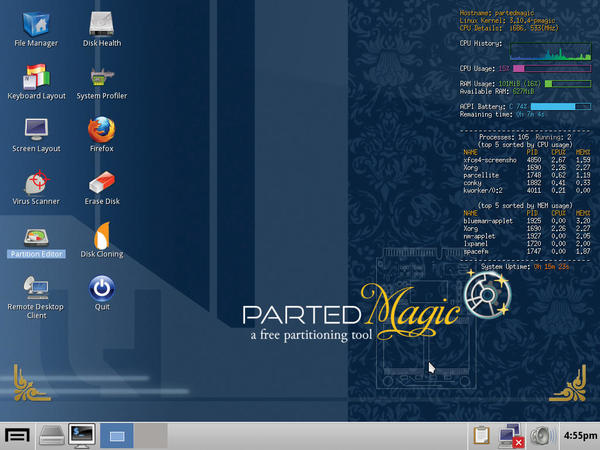
Parted Magic then boots into a somewhat antique-looking graphical system with a number of program icons on the desktop. The most important icons are Disk Cloning, Partition Editor, Erase Disk, Disk Health and – if you use Windows – Virus Scanner (Figure 1).
System Check
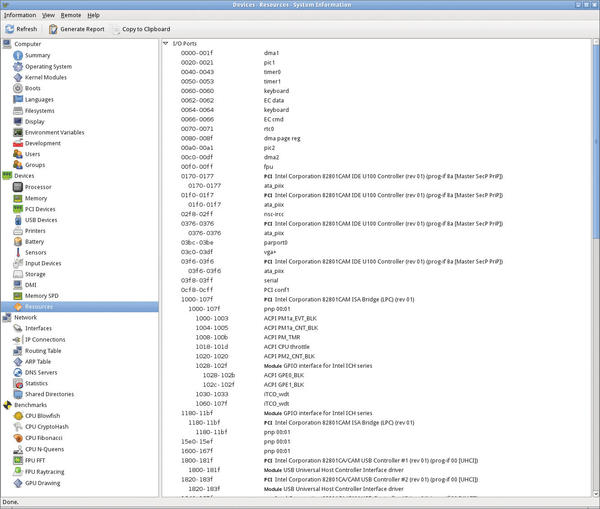
To help you troubleshoot hardware defects in case of inexplicable system behavior, Parted Magic offers a range of tools for checking system integrity. Pressing the System Profiler icon first shows you the details of the detected hardware. The program also supports benchmarking against specific routines (Figure 2).
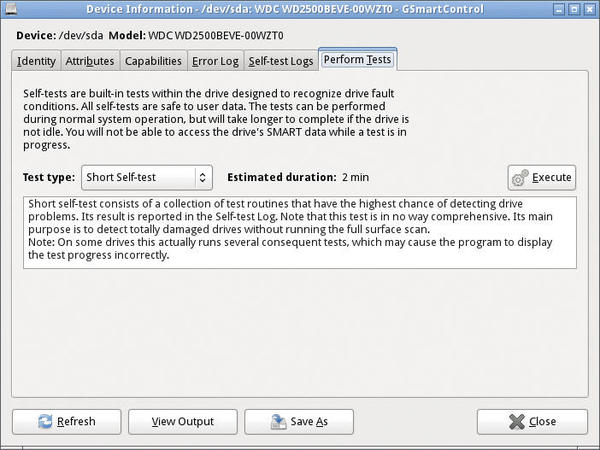
For example, if you suspect – specifically for mobile computers – that overheating of individual components is causing problems, you can use Psensor to read the temperature sensors installed in the computer. If this still doesn’t help you track down the root cause, you might want to check the disk integrity. To do this, press Disk Health, which in turn launches GSmartControl (Figure 3).
ou can then view the faults in the Error Log tab. The Perform Tests tab lets you launch a storage medium test, if in doubt.
In the System Tools menu, you will also find a System Stability Tester (systester) entry, which runs intensive system checks to identify hardware shortcomings. Finally, you can check your audio hardware using Multimedia | Test Audio.
Software Problems
Parted Magic also offers many routines for identifying software problems. The tools that catch the eye here are primarily for Windows systems. For example, the System Tools menu contains two programs: PCLoginNow and Change Windows Password. They allow you not only to change Windows passwords but also reset them if needed. The typical Windows tools include antivirus programs that will rid your Windows computer of malware. Clicking on Virus Scanner launches the ClamAV virus scanner. When you first start the software, it automatically downloads the latest virus patterns.
Another Windows-specific issue is weaknesses of the NTFS filesystem, which tends to become inconsistent in cases of high utilization. To avoid loss of data, the program allows you to Resize NTFS with Bad Sectors in the System Tools menu – even if bad sectors are found. For Linux, Parted Magic offers the Grub Doctor tool, which allows you to repair a broken GRUB2 configuration.
Data Backup
In addition to regular backups, cloning the system partition could also be a useful approach – for example, to restore broken installations at the press of a button. Cloning grabs all the contents of a disk or partition without modifications or deletions so you can, for example, replace a hard disk without reinstalling and reconfiguring the operating system. Parted Magic comes with the Clonezilla, Ghost 4 Linux, and Partition Image tools in the System Tools menu for this task.
Although Clonezilla exclusively creates unchanged images of a disk or partition and puts them on the target in a few steps using a slightly rustic CLI-based interface, Ghost 4 Linux covers a wide spectrum of functions. In addition to sector-wise copying of data, you can also back up individual files from partitions; the software supports an impressive number of different filesystems here. Additionally, Ghost 4 Linux allows you to save and restore backups over the network.
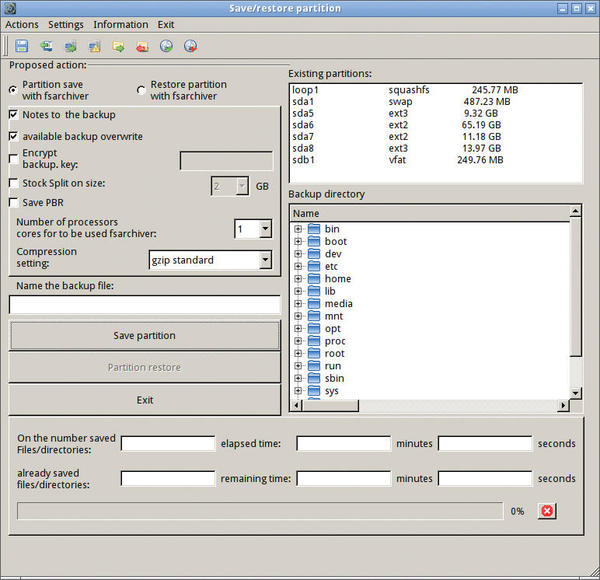
Finally, Partition Image provides similar functionality to Clonezilla and an equally rustic-looking surface. The tool also allows you to use network shares but will also back up and restore the master boot record of a hard disk, if needed. The File System Archiver is a program for backing up partitions; it not only comes with a graphical interface, but can also handle various filesystems, and it lets you encrypt archives (Figure 4).
The somewhat ancient Unstoppable Copier for Linux lets you copy individual file sets; on request, the software takes file trees into consideration and lets you know if it failed to copy files because of faulty integrity.
Wow Effect
The GEncFS tool in Parted Magic lets you manage encrypted partitions. Although the program does not allow you to encrypt conventional partitions, it does give you an easy option for mounting previously encrypted partitions on the current system.
If you intend to work with disk encryption in the future, TrueCrypt in Parted Magic also gives you one of the best encryption tools on the market. The software encodes your data securely and also offers an easily usable graphical interface for newcomers without a deeper knowledge of cryptographic methods.
Partitioning
One of the main tasks of Parted Magic is to edit the setup of existing hard disks and SSD partitions. The distribution primarily provides GParted for this purpose. The tool not only creates, modifies, or deletes partitions, it also changes their size. Additionally, GParted lets you move, test, and format individual partitions. The software supports an impressive number of filesystems.
Data Restore
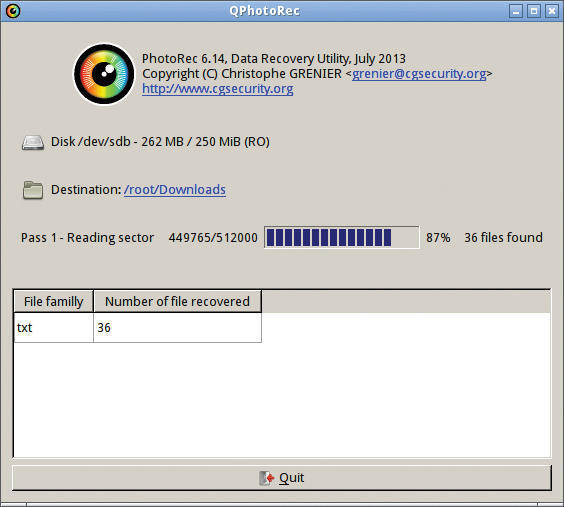
To help you restore accidentally deleted data, Parted Magic includes PhotoRec and its graphical counterpart, QPhotoRec, which are two extremely powerful utilities. QPhotoRec is still in development and therefore does not yet offer the full functionality, as indicated on the welcome screen. However, you can use it on existing partitions to reconstruct supposedly deleted data. Like its command-line counterpart, QPhotoRec supports various filesystems together (Figure 5).
However, to date, you cannot choose the criteria for reconstructing your data, such as the type.
TestDisk is another powerful tool for data reconstruction in Parted Magic. Unlike PhotoRec, TestDisk is designed to recover deleted or damaged disk partitions. It supports the filesystems used by today’s most common operating systems. The software not only helps you restore the partition as such, it also reconstructs damaged boot sectors and identifies the Linux filesystem superblock. It also can copy reconstructed data sets, again supporting all popular filesystems. This means that you can even recover data from USB flash drives or memory cards. Reminiscent of the DOS age, the TestDisk interface looks antiquated; however, it intuitively opens up the individual functions of the program with just a few user-selectable options.
Secure Erase
Secure deletion of entire data media is becoming increasingly important. If you want to sell a used hard drive or dispose of an old PC, for example, you should be aware that all your data is still on the storage medium, even after formatting. To prevent abuse, you must delete the disk securely so that even special programs like TestDisk and PhotoRec have no way of recovering them. Because of the development of mass storage technologies in recent years, the cards have been reshuffled: Along with traditional hard drives, more computers now also contain SSDs, which cannot be securely deleted with conventional methods because of a completely different storage technology.
Conventional hard drives can be deleted securely by completely overwriting all the sectors with randomly generated strings to prevent reconstruction, even using a magnetic resonance microscope, except for a few file fragments. This explains why countless programs implement different regulatory standards for secure data destruction. The disadvantage of all these methods is the enormous time required to erase high-capacity mass storage devices. In some cases, complete overwriting of a large hard disk can take several days.
Modern mass storage devices based on flash memory are not suitable for this type of secure deletion because deletion programs for magnetic disks produce a very large number of writes while overwriting; this process overloads the memory modules of a fast SSD because they can only tolerate a limited number of write cycles.
The most reliable way of resetting an SSD to its factory condition, independently of the manufacturer and type, is to use Secure Erase. This resets the list of unused and used blocks managed on the SSD controller and completely deletes the cells by marking all memory areas of the SSD as unassigned. Unlike magnetic media, file fragments existing in the individual memory cells cannot be reconstructed for SSDs using conventional technology.
Linux has used the hdparm command-line tool for some time for safe deletion. However, it is very inconvenient in use and requires several steps. You can achieve a similar effect if you repartition and format the SSD, creating an ext4 filesystem with the mke2fs command. From version 1.41.10, it automatically deletes all data through an ATA TRIM when reformatting the SSD. However, the prerequisite is that the SSD also supports ATA TRIM.
Parted Magic makes this process much simpler: You just need to press Erase Disk to pop up a window with several options for secure deletion of data medium (Figure 6).
The delete options offered draw on the operating system’s internal commands; for example, selecting the Internal Secure Erase command writes zeros to entire data area button launches hdparm with the appropriate options. Later in the deletion process, the tool prompts you to choose the medium to be erased, and the front end displays all devices that support the corresponding ATA command (i.e., both SSDs and hard disks). The disk erase starts after you make your selection.
Note that some computers implement a freeze-lock routine in the BIOS that blocks a drive against the use of Secure Erase. In this case, Parted Magic offers to switch the computer to sleep mode so that, when it wakes up, the freeze function is disabled and the Secure Erase command can launch. Then, the routine resets the device, indicating the amount of time required at the start of the action. Depending on the size of the disk, the process can take several hours; when the erase process is concluded, a pop-up appears.
Conclusions
In terms of functionality, Parted Magic goes far beyond what most commercial data medium processing programs offer. The Live distribution is not only the perfect choice for your partitioning, backup, and imaging tasks, it also supports the reconstruction of deleted data or its safe erasure on various filesystems, thanks to the many tools. Finally, Parted Magic also comes with several test routines that help you troubleshoot hardware failures.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.