FSF Publishes New Quick Guide on GPLv3
The quick guide gives a short and understandable explanation of the objectives of version 3 of the GPL; recent discussions on GPLv3 had caused many developers to forget the generic purpose of the license – guaranteeing the freedom of software development.
The document briefly recapitulates what the General Public License (GPL) aims to achieve. The author goes on to explain the changes between versions 2 and 3 of the GPL, and the motivations behind the changes citing three threats to freedom. One of them is tivoization, named after the Tivo digital video recorder that contains GPL’d software but prevents users from modifying the GPL programs by validating a digital signature. The other two threats that led to changes in the GPL are Digital Rights Management and Microsoft’s patent covenenant. The author also refers to interfaces to other licenses. The author of the Quick Guide, Brett Smith from the Free Software Foundation (FSF), has posted the guide on the FSF announce mailing list.
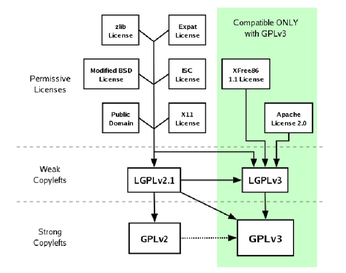
The changes introduced by GPLv3 include new compatibilities to other licenses, as shown by the graphic from the Quick Guide.
The Open Source community can view the text as an impetus to understand the GPL as an opportunity rather than a bone of contention or a threat. Brett’s short, informal announcement closes with the words: "We hope this serves as a useful resource for developers considering adopting GPLv3 for their own projects." Shortly afterwards a senior Red Hat developer commented: "Excellent job, Brett."
The guide is available online, or as a PDF document, and as a zipped tarball in text only format. According to GNU's Who Brett Smith has been with the Free Software Foundation since 2002, and has worked as the Chief Webmaster and Shipping Manager, before becoming the "licensing guru" at the FSF’s licensing and compliance lab which provides “the public with a "knowledge infrastructure" surrounding the GNU GPL and free software licensing, and enforcing the license on FSF-copyrighted software.”
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Debian Unleashes Debian Libre Live
Debian Libre Live keeps your machine free of proprietary software.
-
Valve Announces Pending Release of Steam Machine
Shout it to the heavens: Steam Machine, powered by Linux, is set to arrive in 2026.
-
Happy Birthday, ADMIN Magazine!
ADMIN is celebrating its 15th anniversary with issue #90.
-
Another Linux Malware Discovered
Russian hackers use Hyper-V to hide malware within Linux virtual machines.
-
TUXEDO Computers Announces a New InfinityBook
TUXEDO Computers is at it again with a new InfinityBook that will meet your professional and gaming needs.
-
SUSE Dives into the Agentic AI Pool
SUSE becomes the first open source company to adopt agentic AI with SUSE Enterprise Linux 16.
-
Linux Now Runs Most Windows Games
The latest data shows that nearly 90 percent of Windows games can be played on Linux.
-
Fedora 43 Has Finally Landed
The Fedora Linux developers have announced their latest release, Fedora 43.
-
KDE Unleashes Plasma 6.5
The Plasma 6.5 desktop environment is now available with new features, improvements, and the usual bug fixes.
-
Xubuntu Site Possibly Hacked
It appears that the Xubuntu site was hacked and briefly served up a malicious ZIP file from its download page.