SELinux Sandbox for Untrusted Programs
The security framework SELinux is set to offer a Sandbox in which applications deemed insecure can be partitioned off from other system areas.
Red Hat colleagues Dan Walsh and Eric Paris have designed an additional security tool. SELinux project leader Walsh describes the functionality and development of this tool in a detailed blog entry. The main idea: for SELinux to limit the actions an application can perform and to confine untrusted binaries. This way, users should be able to work with programs and data that are not considered 100% secure.
The developers were inspired to create a sandbox to execute these security measures using the SELinux policies via a query on the Linux core list. Walsh describes: "The bug report talked about confining grep, awk, ls ... The idea was couldn't we stop the grep or the mv command from suddenly opening up a network connection and copying off my /etc/shadow file to parts unknown.“ Regarding further application areas, Walsh sees GRID jobs as potential danger, they might become Spam Bots or attack systems in some other form.
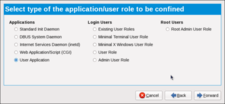 The Sandbox is just ten steps away: Dan Walsh chose "User Applications“ for the Sandbox because the security tool is intended for the user as well as the administrator.
The Sandbox is just ten steps away: Dan Walsh chose "User Applications“ for the Sandbox because the security tool is intended for the user as well as the administrator.
According to Walsh, only 10 clicks were needed to write the policy with the GUI program from Fedora 11. He delivers interested parties precise instructions. In addition to the policy, the “usr/bin/sandbox” tool was written in order to route contents into the Sandbox. One issue with the current version has not yet been fully dealt with: “My current intention with sandbox is not to handle X Apps, since these apps want to write all over the home directory ~/.gconf, ~/gnome., ~/.config ... and all over /tmp, along with use privs to talk to the X Server. I have some ideas on this for the future that I hope to experiment with.”
In a message on the Linux kernel list, Eric Paris introduces a simple application example and invites users to share their experiences. “Check it out, SELinux confinement made easy."
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.
