Getting started with the ELK Stack monitoring solution
Security
The last step is to introduce some security to the stack. Until now, if you enabled access to the stack from all networks, it would mean that anyone could mess with the data. The ELK base configuration does not include any kind of access restrictions, but you can add security through plugins. Two options are the paid Elastic X-Pack Security plugin [4] and the OpenDistro [5] security plugin.
It is worth noting that another option would be to use a proxy service like Apache or Nginx to enforce authorization, but for consistency, I'll stick with a dedicated solution.
The basic scenario is, a user presents credentials that are verified against access backends. When the user's identity is confirmed, the security plugin assigns privileges and roles for the user (Figure 5).
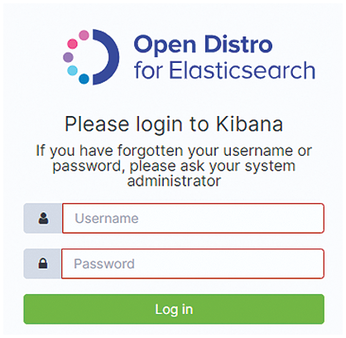
When the OpenDistro plugin is enabled, Kibana presents a login panel (Figure 6).
The configuration for the OpenDistro plugin is stored in a few YAML files in /usr/share/elasticsearch/plugins/opendistro_security/securityconfig/.
As you can see in Listing 16, the YAML file for the security plugin is organized by user account. The hash is an encrypted password generated with the hash.sh script, which is located in the tools subdirectory of the plugin directory. The opendistro_security_roles entry lets you specify any of the predefined roles. Most of the roles are self explanatory, but a word is needed for the logstash role, since it also includes permissions to write Beats indices. If you want to create your own roles, you have to modify the action_groups.yml, roles.yml, and roles_mapping.yml file, which are located in the plugin's securityconfig subdirectory. The config file can also refer to roles assigned in an authentication system such as LDAP or ActiveDirectory.
Listing 16
internal_users.yml
01 # All passwords are: 02 # qwerty 03 _meta: 04 type: "internalusers" 05 config_version: 2 06 07 admin: 08 hash: "$2y$12$N5/i8SBuGv9c8vI5fYNWFe2otKwYPbAfBpNObFjCDpRJQp0k55bfC" 09 reserved: true 10 hidden: true 11 opendistro_security_roles: 12 - all_access 13 description: "Demo admin user" 14 15 kibanaserver: 16 hash: "$2y$12$N5/i8SBuGv9c8vI5fYNWFe2otKwYPbAfBpNObFjCDpRJQp0k55bfC" 17 reserved: true 18 hidden: false 19 opendistro_security_roles: 20 - kibana_server 21 description: "Demo kibanaserver user" 22 23 kibana: 24 hash: "$2y$12$N5/i8SBuGv9c8vI5fYNWFe2otKwYPbAfBpNObFjCDpRJQp0k55bfC" 25 reserved: false 26 opendistro_security_roles: 27 - kibana_user 28 - readall_and_monitor 29 description: "Demo kibana user" 30 31 logstash: 32 hash: "$2y$12$N5/i8SBuGv9c8vI5fYNWFe2otKwYPbAfBpNObFjCDpRJQp0k55bfC" 33 reserved: true 34 hidden: false 35 opendistro_security_roles: 36 - logstash 37 description: "Demo Logstash & Beats user"
You can mark a user, role, role mapping, or action group as reserved. Resources that have the reserved flag set to true can't be changed using the REST API or Kibana. Reserved resources are not returned by the REST API and are not visible in Kibana.
In order to further harden your ELK stack, you can generate certificates to use with SSL and enable them in Elasticsearch, then add user credentials to the Kibana server as well as all beats. In the long run, however, it is a good idea to plug your stack into a company authentication service, such as Okta or LDAP.
Summary
ELK is an amazing solution that allows users to swiftly explore the status of the infrastructure. Although it was originally designed to handle logging, with later iterations and plugins, it has become a fully functional MAL tool (Monitoring-Alerting-Logging). This paper has touched on a few of the many potential options. Other notable features include fully configurable alerting, machine learning, anomaly detectors, and a performance analyzer.
Infos
- ELK Stack: https://www.elastic.co/elastic-stack
- Ansible: https://www.ansible.com/
- grok Filter: https://github.com/logstash-plugins/logstash-patterns-core/blob/master/patterns/grok-patterns
- X-Pack Security Plugin: https://www.elastic.co/guide/en/elasticsearch/reference/current/setup-xpack.html
- OpenDistro: https://opendistro.github.io/for-elasticsearch-docs/
- Code in this Article: https://github.com/szandala/ELK
« Previous 1 2 3
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.