Brad Spengler Exposes Exploit in Linux Kernel 2.6.31
The developer behind the grsecurity.net security portal, Brad Spengler, has released videos on the Web that demonstrate a security hole in the current Linux kernel.
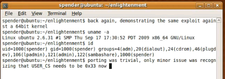
Brad Spengler (alias Spender) is a known entity in the Linux security field. Revealing his videos on his YouTube channel certainly lends his case credibility. The videos show that the exploit uses a buffer overflow in the perf_counter after a kernel crash, which also bypasses SE Linux.
A recent followup to Spengler's video for a 32-bit system is one for a 64-bit Ubuntu exploit. He intends to publish details soon. Fortunately the exploit is currently not freely circulating.
Comments
comments powered by DisqusSubscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.
-
CIQ Releases Compatibility Catalog for Rocky Linux
The company behind Rocky Linux is making an open catalog available to developers, hobbyists, and other contributors, so they can verify and publish compatibility with the CIQ lineup.
-
KDE Gets Some Resuscitation
KDE is bringing back two themes that vanished a few years ago, putting a bit more air under its wings.

How to mitigate such risks..
At our IT Security Conference, AthCon, www.athcon.org which will be hosted in Athens, Greece in Q2 2010, we'll be discussing how to mitigate such vulnerabilities in production code & how to thwart null pointer dereference vulnerabilities once & forever.
- AthCon team.