Making PDFs More Secure in LibreOffice Writer
LO Writer – PDF Security

© Lead Image © Fotoflash, Fotolia.com
Depending on your needs, LibreOffice Writer offers varying degrees of security for PDFs.
PDFs date from a less security-conscious era than our own. However, over the years, the PDF format has added security features. Today, if you need security, you have two choices: passwords and permissions for casual security of digital certificates or GNU Privacy Guard (GPG) keys for serious encryption. Both are available from tabs on LibreOffice's PDF Options window when exporting to PDF.
Passwords and Permissions
PDFs have their own system of passwords and permissions, which are available from File | Export As | Export As PDF… | PDF Options | Security (Figure 1). To set them up, begin by entering a password to open the exported file, and a second one to alter the permissions (in other words, how the files can be used). After the second password is entered, three kinds of permissions are available: Printing, Changes, and Contents. Together, options can be as strict as allowing a user only to view the file, as loose as allowing any user to alter the file at will, or something in-between.
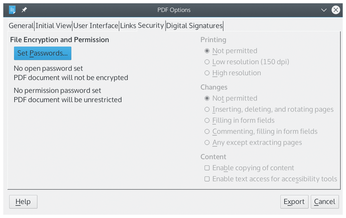 Figure 1: The Security tab in the PDF Options window offers a casual grade of security with a variety of options.
Figure 1: The Security tab in the PDF Options window offers a casual grade of security with a variety of options.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
KDE Linux Drops AUR
KDE Linux developers have dropped the Arch User Repository from the build pipeline due to security concerns; other distributions should consider doing the same.
-
California May Exempt Linux from Its Age-Verification Law
After backlash from the Linux community, California may be backing off on its promise to force all operating systems to verify age, but one platform may still have to comply.
-
Another Logic Bug Found in Linux Kernel
Qualys has discovered a vulnerability in the Linux kernel that can be used to elevate standard user privileges.
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
