A partial replacement for PGP/GPG
Command Line – Modern File Encryption

© Lead Image © photonphoto, 123RF.com
Age, a modern encryption tool, could soon replace PGP and GPG when it comes to file encryption.
If you encrypt, you are probably familiar with Pretty Good Privacy (PGP) [1] or its clone GNU Privacy Guard (GPG). Most likely, you have used one of these tools to generate public and private keys and to encrypt email and files. The Free Software Foundation explains these tools in its Email Self-Defense Guide as a first step towards privacy [2]. However, despite PGP and GPS being ubiquitous when it comes to privacy, some people believe that these tools are counter-productive and little more effective than the feeble default protection available for PDF files when it comes to modern computing. Ironically, as PGP and GPG become more widely used, some security experts are advocating for their replacement with Actual Good Encryption (age), at least for file encryption [3].
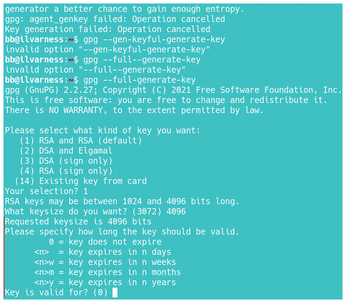
Why do some security experts claim that PGP and GPG are obsolete? To begin with, PGP and GPG have long public keys that can be difficult to work with when space is limited, and copying them accurately by hand is difficult. In particular, they can be difficult to configure, even when the simple configuration wizard is used (Figure 1). When generating a key, PGP and GPG require numerous choices, including the encryption method, the key size, and how long the key is valid. Even a moderately skilled user can be hard-pressed to answer such questions intelligently. As a result, users may simply fall back on the defaults, although ignorance and security are hardly compatible. Many users, too, complain about having to move the cursor around to generate sufficient randomness – and, the longer the key, the longer it takes to generate the randomness. To further add to the confusion, PGP and GPG do too many things, such as signing services and key management, that many users have no interest in, which can add to the confusion.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Foundation Report Indicates AI Driving Tech Hiring
Within growing security and skills gaps, AI has been found to be a positive driving force behind tech hiring trends in Europe.
-
United Nations Open Source Portal Goes Live
A new open source portal seeks to coordinate and scale open source efforts across the United Nations system.
-
KDE Linux Drops AUR
KDE Linux developers have dropped the Arch User Repository from the build pipeline due to security concerns; other distributions should consider doing the same.
-
California May Exempt Linux from Its Age-Verification Law
After backlash from the Linux community, California may be backing off on its promise to force all operating systems to verify age, but one platform may still have to comply.
-
Another Logic Bug Found in Linux Kernel
Qualys has discovered a vulnerability in the Linux kernel that can be used to elevate standard user privileges.
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.