Securing the Linux kernel with lockdown mode
The term lockdown does not have particularly positive connotations at present, but prior to COVID-19, the word was used in a very positive context as a term for air-tight security. Several months ago, Linux boss Linus Torvalds accepted a series of patches for the Linux kernel that introduced what is known as lockdown mode. Lockdown mode puts limits on the power of system users – including the once-all-powerful system administrator (root) account. Putting constraints on the root account might seem very strange to Unix/Linux veterans, but security experts are happy to see this powerful new feature in our dangerous times.
Long Time Ago
When Linus finally incorporated the lockdown patches into the official kernel at the end 2019, many observers described lockdown mode as a revolutionary new feature. But lockdown mode is not a new invention. In fact, the work on implementing the function took almost seven years. And for most of that time, the Linux kernel developers were arguing – sometimes heatedly – about the right way to do it (Figure 1). See the box entitled "Linux Security Modules" for more on a solution that arose from that heated debate.
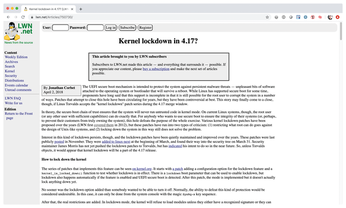 Figure 1: Even in mid-2018, the developers were still debating fiercely about how to implement lockdown in a sensible way.
Figure 1: Even in mid-2018, the developers were still debating fiercely about how to implement lockdown in a sensible way.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Nitrux 6.0 Now Ready to Rock Your World
The latest iteration of the Debian-based distribution includes all kinds of newness.
-
Linux Foundation Reports that Open Source Delivers Better ROI
In a report that may surprise no one in the Linux community, the Linux Foundation found that businesses are finding a 5X return on investment with open source software.
-
Keep Android Open
Google has announced that, soon, anyone looking to develop Android apps will have to first register centrally with Google.
-
Kernel 7.0 Now in Testing
Linus Torvalds has announced the first Release Candidate (RC) for the 7.x kernel is available for those who want to test it.
-
Introducing matrixOS, an Immutable Gentoo-Based Linux Distro
It was only a matter of time before a developer decided one of the most challenging Linux distributions needed to be immutable.
-
Chaos Comes to KDE in KaOS
KaOS devs are making a major change to the distribution, and it all comes down to one system.
-
New Linux Botnet Discovered
The SSHStalker botnet uses IRC C2 to control systems via legacy Linux kernel exploits.
-
The Next Linux Kernel Turns 7.0
Linus Torvalds has announced that after Linux kernel 6.19, we'll finally reach the 7.0 iteration stage.
-
Linux From Scratch Drops SysVinit Support
LFS will no longer support SysVinit.
-
LibreOffice 26.2 Now Available
With new features, improvements, and bug fixes, LibreOffice 26.2 delivers a modern, polished office suite without compromise.
