Securing the Linux kernel with lockdown mode
The term lockdown does not have particularly positive connotations at present, but prior to COVID-19, the word was used in a very positive context as a term for air-tight security. Several months ago, Linux boss Linus Torvalds accepted a series of patches for the Linux kernel that introduced what is known as lockdown mode. Lockdown mode puts limits on the power of system users – including the once-all-powerful system administrator (root) account. Putting constraints on the root account might seem very strange to Unix/Linux veterans, but security experts are happy to see this powerful new feature in our dangerous times.
Long Time Ago
When Linus finally incorporated the lockdown patches into the official kernel at the end 2019, many observers described lockdown mode as a revolutionary new feature. But lockdown mode is not a new invention. In fact, the work on implementing the function took almost seven years. And for most of that time, the Linux kernel developers were arguing – sometimes heatedly – about the right way to do it (Figure 1). See the box entitled "Linux Security Modules" for more on a solution that arose from that heated debate.
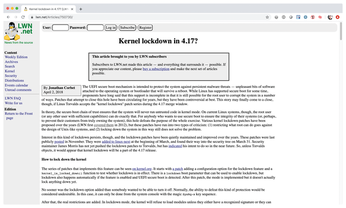 Figure 1: Even in mid-2018, the developers were still debating fiercely about how to implement lockdown in a sensible way.
Figure 1: Even in mid-2018, the developers were still debating fiercely about how to implement lockdown in a sensible way.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Two New Distros Adopt Enlightenment
MX Moksha and AV Linux 25 join ranks with Bodhi Linux and embrace the Enlightenment desktop.
-
Solus Linux 4.8 Removes Python 2
Solus Linux 4.8 has been released with the latest Linux kernel, updated desktops, and a key removal.
-
Zorin OS 18 Hits over a Million Downloads
If you doubt Linux isn't gaining popularity, you only have to look at Zorin OS's download numbers.
-
TUXEDO Computers Scraps Snapdragon X1E-Based Laptop
Due to issues with a Snapdragon CPU, TUXEDO Computers has cancelled its plans to release a laptop based on this elite hardware.
-
Debian Unleashes Debian Libre Live
Debian Libre Live keeps your machine free of proprietary software.
-
Valve Announces Pending Release of Steam Machine
Shout it to the heavens: Steam Machine, powered by Linux, is set to arrive in 2026.
-
Happy Birthday, ADMIN Magazine!
ADMIN is celebrating its 15th anniversary with issue #90.
-
Another Linux Malware Discovered
Russian hackers use Hyper-V to hide malware within Linux virtual machines.
-
TUXEDO Computers Announces a New InfinityBook
TUXEDO Computers is at it again with a new InfinityBook that will meet your professional and gaming needs.
-
SUSE Dives into the Agentic AI Pool
SUSE becomes the first open source company to adopt agentic AI with SUSE Enterprise Linux 16.

