RetroShare
Is a private network useful for privacy and security?
ByRetroShare helps you create a private, decentralized friends-to-friends network with encrypted communications, but how much does that increase security and privacy?
With the need for greater privacy and security measures becoming a given, RetroShare is newly timely. First developed 10 years ago, RetroShare sets up a private network and provides a graphical interface for encryption, which greatly simplifies privacy for users who might be too intimidated or too uncertain of their knowledge to take the measures for themselves. The question, though, is whether the solution ignores other security measures and is too limited to be practical.
RetroShare is reminiscent of Kontact, the KDE shell that groups personal information tools – email, contacts, calendars, to-do lists and notes – in a single window. In fact, RetroShare overlaps with Kontact in such features as email and news.
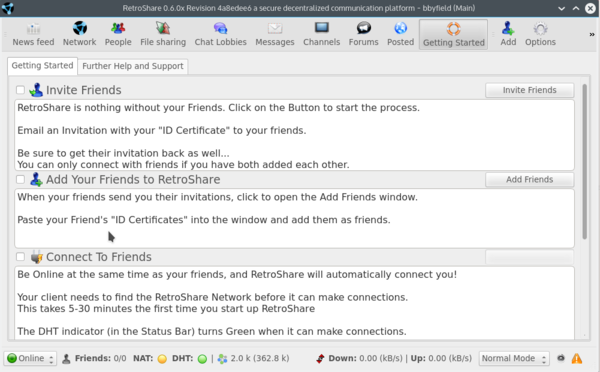
The difference is that, rather than personal information, RetroShare focuses on different means of communication, including not only email and news, but also file sharing, chat, and forums – essentially any online interaction that might risk privacy and security (Figure 1).
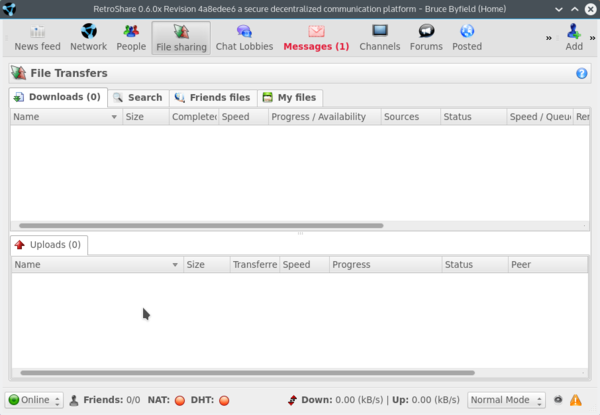 Figure 1: Started in 2006, RetroShare offers one possible solution to today’s security and privacy problems.
Figure 1: Started in 2006, RetroShare offers one possible solution to today’s security and privacy problems.
The Security of Private Networks
RetroShare resembles an updated version of darknets, the private networks created 40 years ago on ARPANET. The modern Internet, of course, is much larger and more complicated than its ancestor, but by communicating only with those you specifically invite, you automatically limit intrusions. Social engineering, such as identity theft or simply placing trust in the wrong people remains a problem, but that is true of most security measures. At least RetroShare includes a graphical indicator of each user’s reputation, which provides some idea of how much they should be trusted.
The first time you log in to RetroShare, you are required to create a new profile. Those who have tried PGP or some variant like GnuPG will recognize the request to move the mouse around in order to create as much randomness as possible while generating a public key (Figure 2), but nothing in the window indicates exactly what is being done. The generation of a passphrase is simply incorporated into the interface and work flow.
Once you have created your profile, you might want to add an Avatar; however, before you can use your private network, someone else needs to belong to it. If you click the Getting Started icon, you can read brief but mostly adequate instructions for adding friends (Figure 3). Using these instructions, click the Add icon to run the Connect Friend menu. RetroShare includes a sample email invitation that invites friends to install it, which makes adding friends as simple as possible.
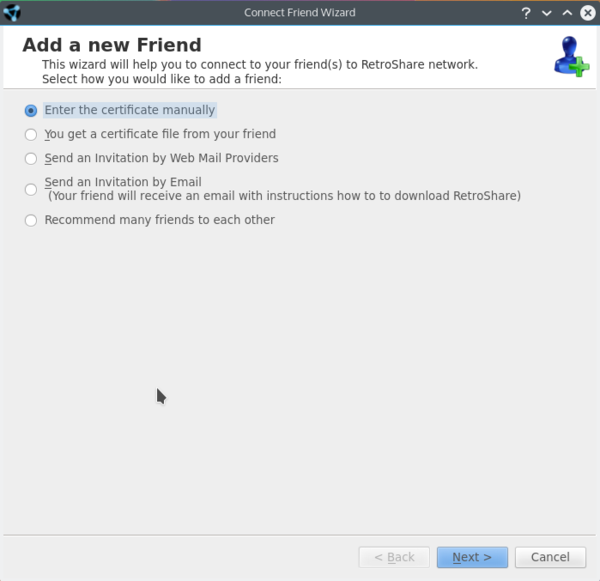
Note, though, that, contrary to the constructions, you cannot paste a friend’s public key into the wizard. Instead, you must either enter the certificate manually – which is impractical if the certificate is more than a couple of dozen characters, as it generally is – or else enter it from a file (Figure 4).
When you log in to RetroShare, all members of your network who are currently online are available, although they might have used the status bar at the bottom of the window to indicate they are Busy or Away and not accepting communications. You can broadcast messages to everyone in your network by clicking the Network icon or set up a selected group to talk to with the Chat Lobbies icon. Similarly, you can share files or links with some or all of those on the network. Encryption is used in all interactions, which bars outsiders from seeing them. You also have the option of disabling access to some of RetroShare’s features using the Permissions tab in the Options dialog. The project pages suggest that a private network is more interesting if it has a minimum of five members, and the more the better.
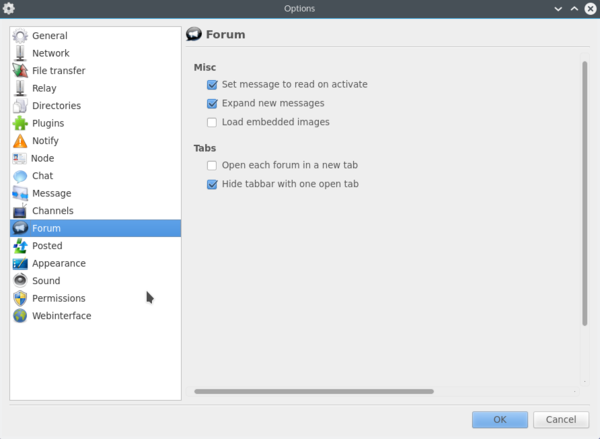
However, before you start inviting too many friends into your network, spend some time investigating RetroShare’s Options. Many are cosmetic or a matter of preference, but many could potentially affect security (Figure 5). For example, do you really want friends to relay your communications to other friends? What about friends of friends of friends? As friends start to sign up, you should also consider which friends you want in each chat lobby.
Problems with Other Security Measures
“Is RetroShare private and secure?” asks a question in the project’s FAQ. “Of Course RetroShare is private and secure,” is the answer. However, given that the answer goes on to talk entirely about private networks and encryption, it is clear that RetroShare relies on these two features at the expense of others.
The two are a powerful combination, but their effectiveness has its limitations. Unlike Tor, RetroShare has no claim to complete anonymity – while those outside a private network may have no access, those within the private network can view each other’s IP addresses. This limitation may matter little in a network of a few friends, but if the network grows into the dozens or hundreds, a user of RetroShare has to be careful about settings and even limit their use of some features if protecting their privacy.
Moreover, the effectiveness of private networks and encryption is marred in RetroShare by gaps in the documentation, especially for advanced or recent features. For example, the latest version is supposed to allow multiple identities with different keys for greater anonymity, but the only indication of this new feature appears to be in the FAQ , and no instructions are visible that even hints at how to implement it.
Just as importantly, other security measures seem to be largely overlooked. In particular, RetroShare’s own password has no limitations on it. No minimal length or combination of cases, characters, numbers, or symbols is required. Yet a weak password could easily make the application vulnerable, all the more so because public keys are stored unencrypted among the options.
Other security gaps are also visible. For instance, although file transfers are confined to a single directory, they are enabled by default. Similarly, hashed files are stored by default for 10 days, and if a firewall is blocking RetroShare’s operations, users are simply advised to open a hole in the firewall. Although encryption generally bars outsiders from reading your communication, you might not want friends of friends reading them.
It is one matter for users to choose such settings for themselves. However, it is an other thing altogether to install with such defaults. A dependable security relies on defense in depth – that is, a variety of security measures – not just a couple of high-profile ones. Dependable security should also enforce the principle of least access, or the limiting of the availability of tools and data to the essentials, and – among other actions – installing with many features turned off and leaving users to decide what they want to use.
Occasionally RetroShare does include more secure defaults, such as not enabling the downloading of embedded images, which are a common vehicle for malware. Yet while RetroShare uses some powerful tools that might very well be sufficient in themselves, users could have more confidence in the application if more security measures were tighter.
The Difficulty of Isolation
RetroShare provides a possible solution to security and privacy issues and deserves credit for making encryption accessible to desktop users. However, I am reminded of commercial services to secure email that sprang up around the time that RetroShare’s development first began. Like RetroShare, these services basically depended on a white list, and anyone not on the list had to request permission to communicate with a user. This practice undoubtedly reduced spam, but it was also undoubtedly a nuisance, and few of these services survived more than a couple of years. They were simply too limited.
The truth is, knowing that common communications are secure may be a relief, but isolating yourself from other exchanges is simply impractical for most users. Although RetroShare may be full-featured, most people generally need privacy and security measures that can deal with unforeseen communications, and not just the expected ones. Nor do many people care to maintain more than one application for one function. For these reasons, RetroShare is a brave effort, but, in the end, an ineffective one.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.