Korset: Linux security thanks to static analysis
Coworkers at the University of Tel Aviv have presented a prototype for a new host-based intrusion detection system (HIDS) for Linux. Named Korset, it uses static code analysis and promises zero failures.
A host-based intrusion system (HIDS) models an application’s behavior and if the behavior deviates from the model, it sends an alarm. Earlier methods of intrusion detection depended either on static data derived from machine learning or on program policies created by developers. In the views of Professor Avishai Wool and kernel developer Ohad Ben-Cohen, the first method is susceptible to false positives and the second one costly.
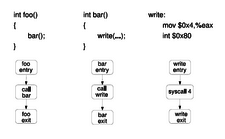
Instead, Wool and Ben-Cohen use a behavioral model automated through static analysis of source code and object files resulting in control flow graphs (CFGs). Since most attacks are accompanied by system calls, the CFGs limit themselves to these calls and document the legitimate pattern for each application. If a program deviates from the pattern, the kernel ends the process.
Korset consists of two parts: a static analyzer in user space and a runtime monitoring agent in the kernel. The analyzer is drawn into the program’s build process and creates a CFG for each executable, object data and library. The Korset runtime monitor is built into the kernel. Once a detected program runs, the agent monitors any resulting system calls and compares them with those of the CFG model.
Wool’s and Ben-Cohen’s report to the Ottawa Linux Symposium 2008 (PDF) includes further details about their work, as does their presentation at the Black Hat US 2008 conference.
A Korset prototype download is available under GPLv3 terms. The developers designate the implementation as pre-alpha software not yet ready for use, but proof-of-concept.
Comments
comments powered by DisqusSubscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.

Won't protect apps that include an interpreter.
Now, if Korset could analyze the script itself, not the interpreter, then you might get more information. But languages like Python and Ruby are so dynamic that static analysis can't usually tell you much, unless you restrict the language.
Not all that useful