Cloud Security
Three encryption tools for the cloud
BySafeguard your cloud storage with some preemptive file encryption. Here are three open source tools that get the job done in Linux.
From a security perspective, cloud storage ought never to have happened. The trouble is, it relies on the ability of users to trust the provider, yet often the only assurance available is the provider’s word. However, the convenience of cloud storage is too great for many companies and individuals to avoid it. Fortunately, security can be regained by users storing only encrypted files.
Numerous tools exist for encrypting in the cloud. Some are proprietary. However, these solutions also require trust -- they only shift the trust requirement to a third party, and basic security requires the user to verify security for themselves.
A better solution is to use open source tools to encrypt files before they are placed in online storage. In Linux, three of the most usable tools for this purpose are EncFS, Cryptomator, and Tahoe-LAFS. As two of the names suggest, each of these treats the online storage as a virtual filesystem, although the quality of them varies considerably.
EncFS
EncFS is used generally to create encrypted virtual filesystems. It can create remote virtual filesystems as easily as local ones if you are using a storage site that syncs a remote directory with a local one. For example, with Dropbox, the command to set everything up would be:
encfs ~/Dropbox/encrypted ~/Private
This command creates the directory for encrypted files in the home directory and another directory for the unencrypted files. The command sets up the encrypted directory by asking a series of questions. You can start with the default paranoia mode by pressing the p key or the expert mode by pressing x and making the choices for encryption manually. The expert questions are clearly explained, so even a novice should have no trouble answering them, if only by accepting the default. Alternatively, you can skip answering the questions by running the command with the --standard option, which uses predefined settings.
The next time users sync with the online storage on Dropbox, the encrypted directory will be added to it. Files added to the /Private directory will automatically be added to ~-Dropbox/-encrypted.
Note, however, that EncFS does not guard against the provider moving or deleting files. As well, when you install the version of EncFS in Debian “stable,” a note from 2014 warns that it is vulnerable to attacks from users with read and write access to the files, including lowering the encryption complexity and using timing analysis. This problem seems to have been addressed in the Testing repository version in the Testing repository, so use that one.
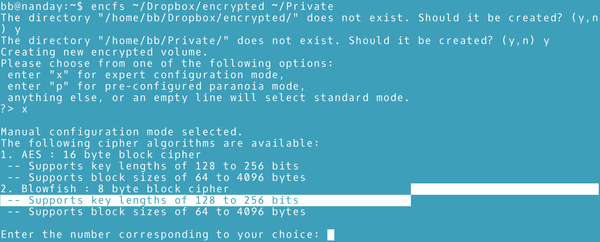 Figure 1: EncFS’s expert mode explains itself well enough that most users should be able to work with it.
Figure 1: EncFS’s expert mode explains itself well enough that most users should be able to work with it.
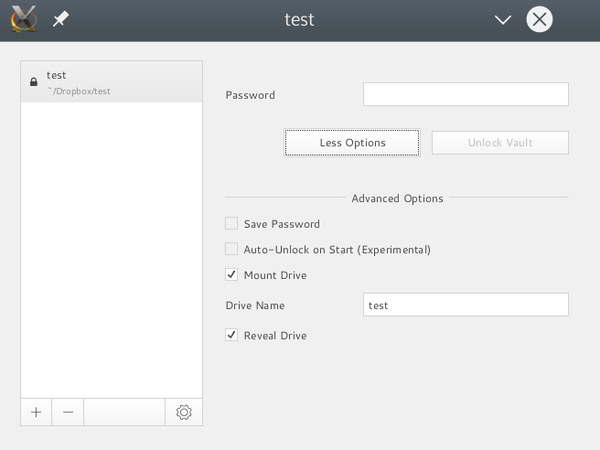
Cryptomator
The workflow for Cryptomator is structured much the same as EncFS. The main difference is some of the jargon -- for example, in Cryptomator, encrypted directories are “vaults.”
Cryptomator’s window opens with the option to create a vault or open one. Naturally, the first time Cryptomator runs, a vault must be created by giving a path and a password. Returning to the opening window, users can open a vault and use the system’s file manager to copy files to the vault. All files added to the vault are encrypted automatically. As with EncFS, a vault placed in the local directory for a storage provider like Dropbox will be uploaded to the cloud when users sync.
Whether you prefer EncFS or Cryptomator depends on your habits. If you want some control of the encryption process, you are likely to prefer EncFS. However, if you prefer desktop apps, you are more likely to favor Cryptomator.
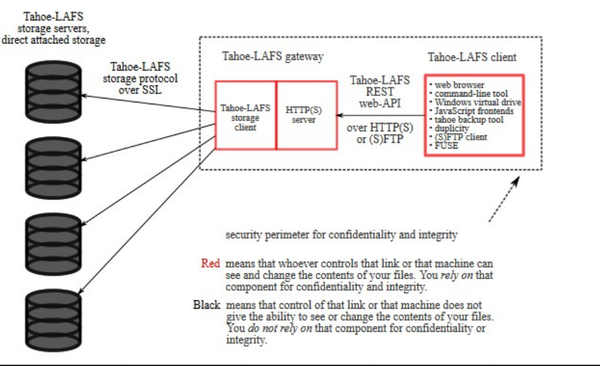
Tahoe-LAFS
Tahoe-LAFS provides the most comprehensive solution. The name is short for “Least Authority FileSystem,” a reference to a classic principle. Basically, Tahoe is designed to give the cloud storage provider as little control over your data as possible
To start with, Tahoe automatically encrypts all files with its a 2000-bit RSA public key. It includes no option for not encrypting files, as well as options for working with Tor.
However, what makes Tahoe stand out is its ability to decentralize files. Users can set up a grid -- a collection of servers -- for storage use. This ability means that a file can actually be stored on more than one server. For instance, users could store part of a file on Dropbox and another part on Google Storage, so that no one service has full control over the file. To de-encrypt and open the file, users must have access to all the storage accounts.
As a bonus, each file is guarded against server failure or any other loss of data. By default, each file has 10 pieces or shares, any three of which are needed to use the file. The majority of shares can actually be lost, and the file is still retrievable. When each file is uploaded, users can adjust the shares to a maximum of 256. Fewer shares require less planning, while more offer greater security. To each location where shares are uploaded, Tahoe adds a file cap, a file for checking the integrity of the encryption key, locating other shares, and retrieving files. In place of user information or permissions, access to the file is governed by knowledge of the encryption key. For further security, uploaded files cannot be edited and must be uploaded again if any changes are made to them. At every step, storage providers have the least possible authority, being reduced to a completely passive role.
In addition to this basic arrangement, Tahoe includes an optional web interface, as well as a utility that informs users if the number of shares falls below the minimum number required for retrieval. Numerous related projects are also available, including a backup tool, a collection of utilities, and plugins for use with other applications, including Puppet.
Tahoe requires strategic planning and can take time to set up before any files can be uploaded. Without well-established policies for the number of shares or the locations for online storage, the result could easily become chaotic. However, once set up, the security provided by Tahoe is second to none.
Other Choices
Encryption choices come and go on Linux. Many of those investigated for this article are no longer being developed. The ones listed here are three with some staying power and provide a tool for all levels of users on public clouds. For private clouds, try Nextcloud.
next page » 1 2
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
KDE Linux Drops AUR
KDE Linux developers have dropped the Arch User Repository from the build pipeline due to security concerns; other distributions should consider doing the same.
-
California May Exempt Linux from Its Age-Verification Law
After backlash from the Linux community, California may be backing off on its promise to force all operating systems to verify age, but one platform may still have to comply.
-
Another Logic Bug Found in Linux Kernel
Qualys has discovered a vulnerability in the Linux kernel that can be used to elevate standard user privileges.
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.