GRUB-free booting
Goodbye Bootloader?

© Photo by Samuel Horn af Rantzien on Unssplash
Linux is in constant flux, which naturally affects the boot process. Bootloaders such as GRUB are slowly being replaced with a faster, more secure boot process.
More than 20 years ago, early adopters of Linux would typically rely on the Linux Loader (LILO) boot manager to fire up their systems. LILO, which began development in 1992 with the last version released in 2015, had one major drawback: It was unable to read filesystems, meaning that it had to know the kernel's precise memory addresses. Every kernel update meant reading the blocks again before the system could boot. Despite this drawback, LILO was easy to configure and did not require filesystem support during the boot process, because it grabbed the kernel directly at the previously defined location on the hard disk (Figure 1).
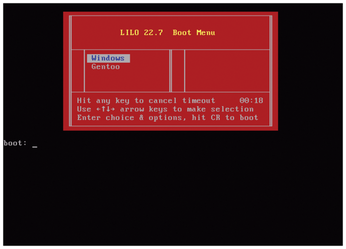 Figure 1: LILO, which did not require filesystem support, was a popular, easy-to-use bootloader at the turn of the millennium.
Figure 1: LILO, which did not require filesystem support, was a popular, easy-to-use bootloader at the turn of the millennium.
At the turn of the millennium, the Grand Unified Bootloader (GRUB) gradually replaced LILO, because it offered more flexibility in terms of filesystems and installation targets. The majority of today's systems boot with the help of GRUB 2, which was first released in 2012. GRUB 2 can handle a wide variety of filesystems, plus encryption, compression, and RAID. For some time now, systems that use systemd to initialize have also been able to opt for systemd-boot [1], which emerged from the Gummiboot bootloader as an alternative.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
KDE Linux Drops AUR
KDE Linux developers have dropped the Arch User Repository from the build pipeline due to security concerns; other distributions should consider doing the same.
-
California May Exempt Linux from Its Age-Verification Law
After backlash from the Linux community, California may be backing off on its promise to force all operating systems to verify age, but one platform may still have to comply.
-
Another Logic Bug Found in Linux Kernel
Qualys has discovered a vulnerability in the Linux kernel that can be used to elevate standard user privileges.
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
